A practical review of suspicious activity detection in money transfer transactions


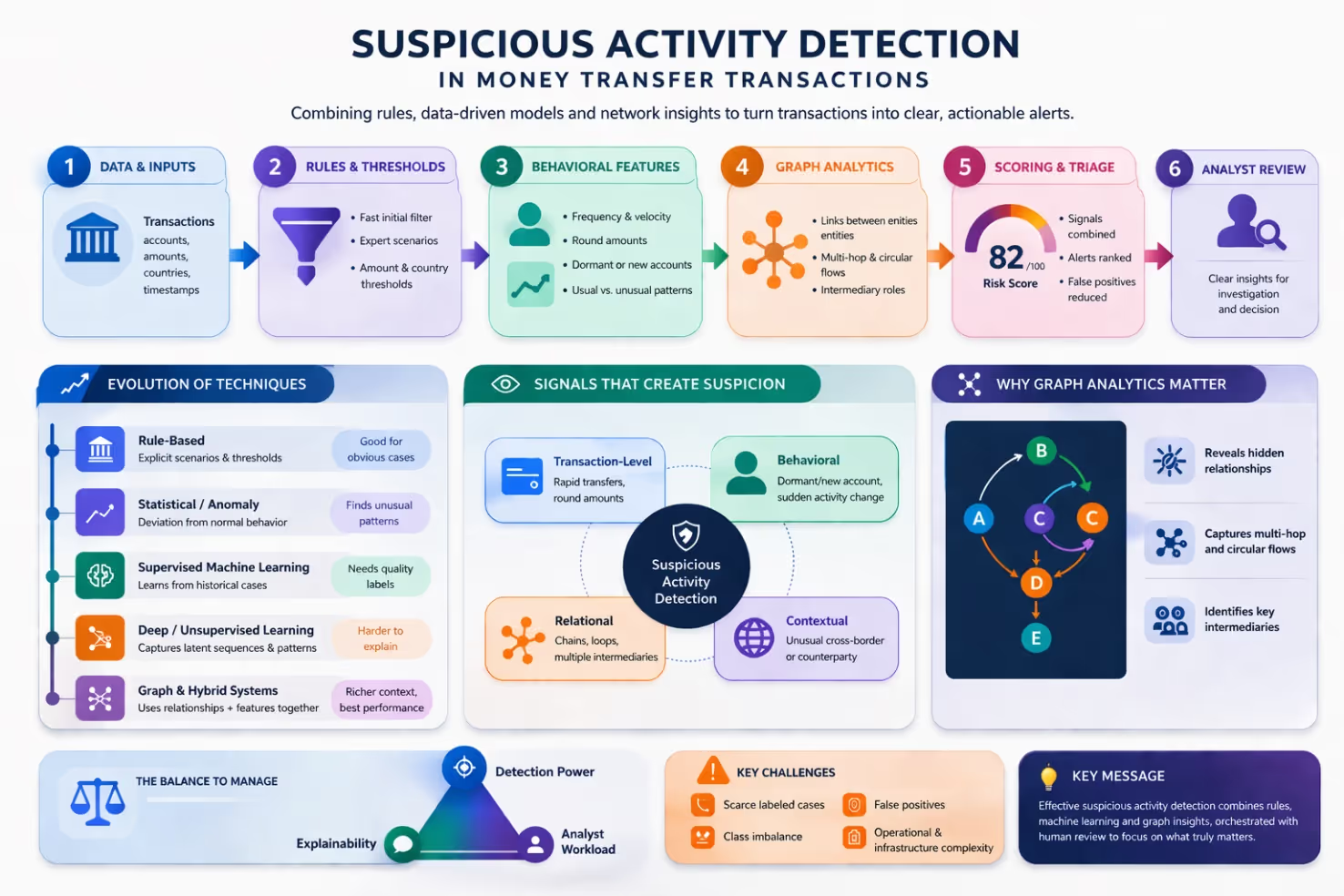
Suspicious transfer detection in financial institutions has evolved far beyond static rules and fixed thresholds, which were simple to deploy but often generated excessive false alerts and were easy to circumvent. Machine learning introduced a more adaptive approach by learning from historical data to better identify and prioritize genuinely risky behavior, while graph analysis added another layer of insight by uncovering hidden network patterns such as circular flows, intermediaries, and coordinated multi-step schemes that isolated transaction screening cannot detect. Today, the main challenge is not only improving detection power but also ensuring transparency, which is why the most effective systems combine rules, statistical models, graph intelligence, and human oversight.
Suspicious activity detection in money transfer transactions has become one of the most difficult operational problems in anti-money laundering. The reason is simple: illicit flows rarely announce themselves as obviously illegal. They are usually embedded in large volumes of normal-looking transfers, spread across accounts, geographies, and time windows, and often mixed with behavior that is commercially plausible on the surface. The literature therefore frames the problem as one of pattern recognition under uncertainty, where the goal is not only to identify unusual events, but also to decide which combinations of events deserve investigation [17, 9, 30, 39].
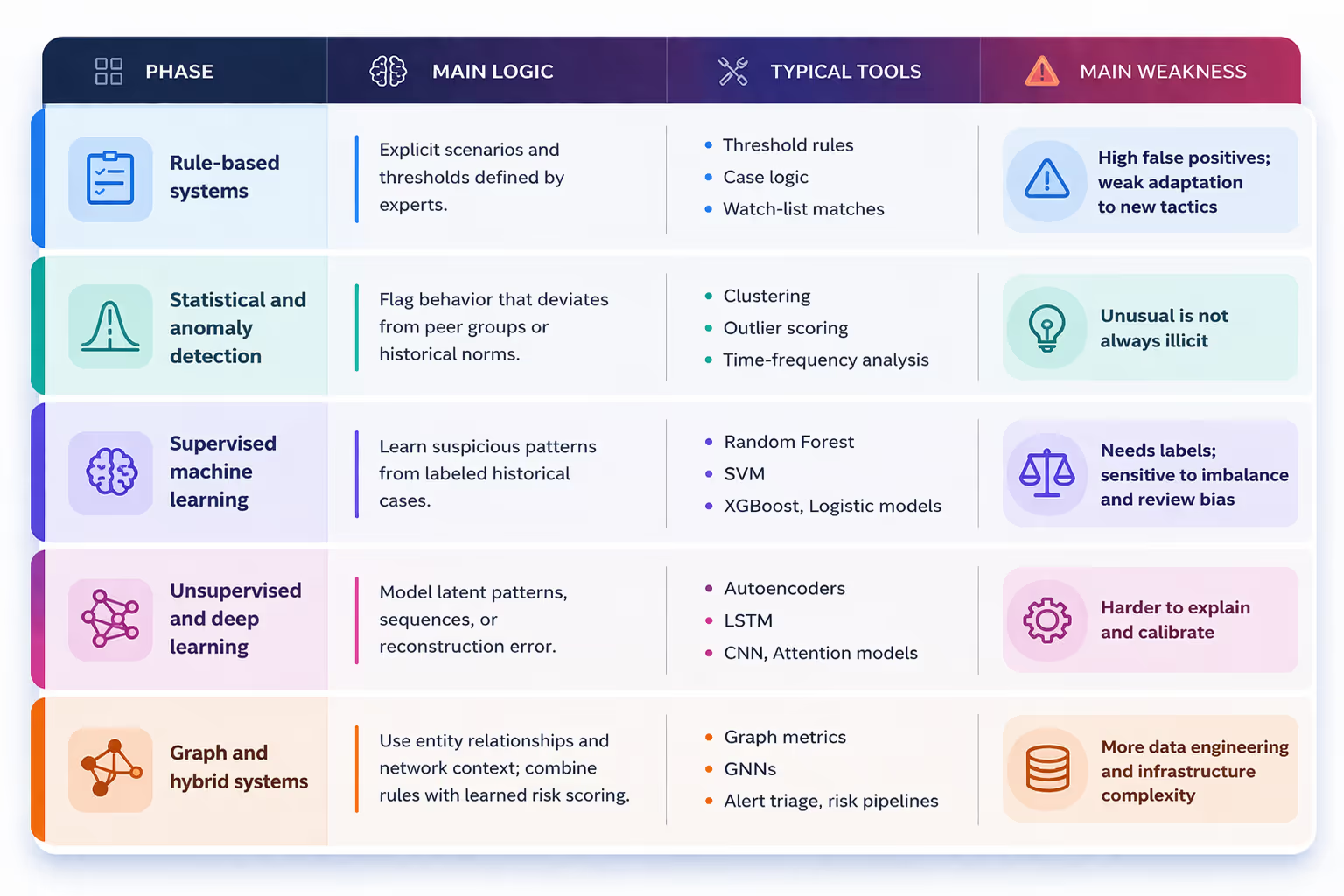
Across the literature, one broad trend is unmistakable. Detection has moved from static thresholds and manually curated rules toward data-driven pipelines that combine behavioral features, anomaly detection, graph analytics, deep learning, and risk scoring. Yet the older approaches have not disappeared. In practice, many institutions still rely on layered systems in which business rules remain the first filter, while machine learning helps rank, suppress, or enrich alerts downstream [3, 6, 10, 17, 22, 31, 33]. That is why a practical state-of-the-art review should not ask which single method is best in the abstract. It should ask which methods solve which part of the monitoring problem, under which data and regulatory constraints.
Figure 2 offers a compact reading of how suspicious signals accumulate from single transfers to analyst-facing alerts.
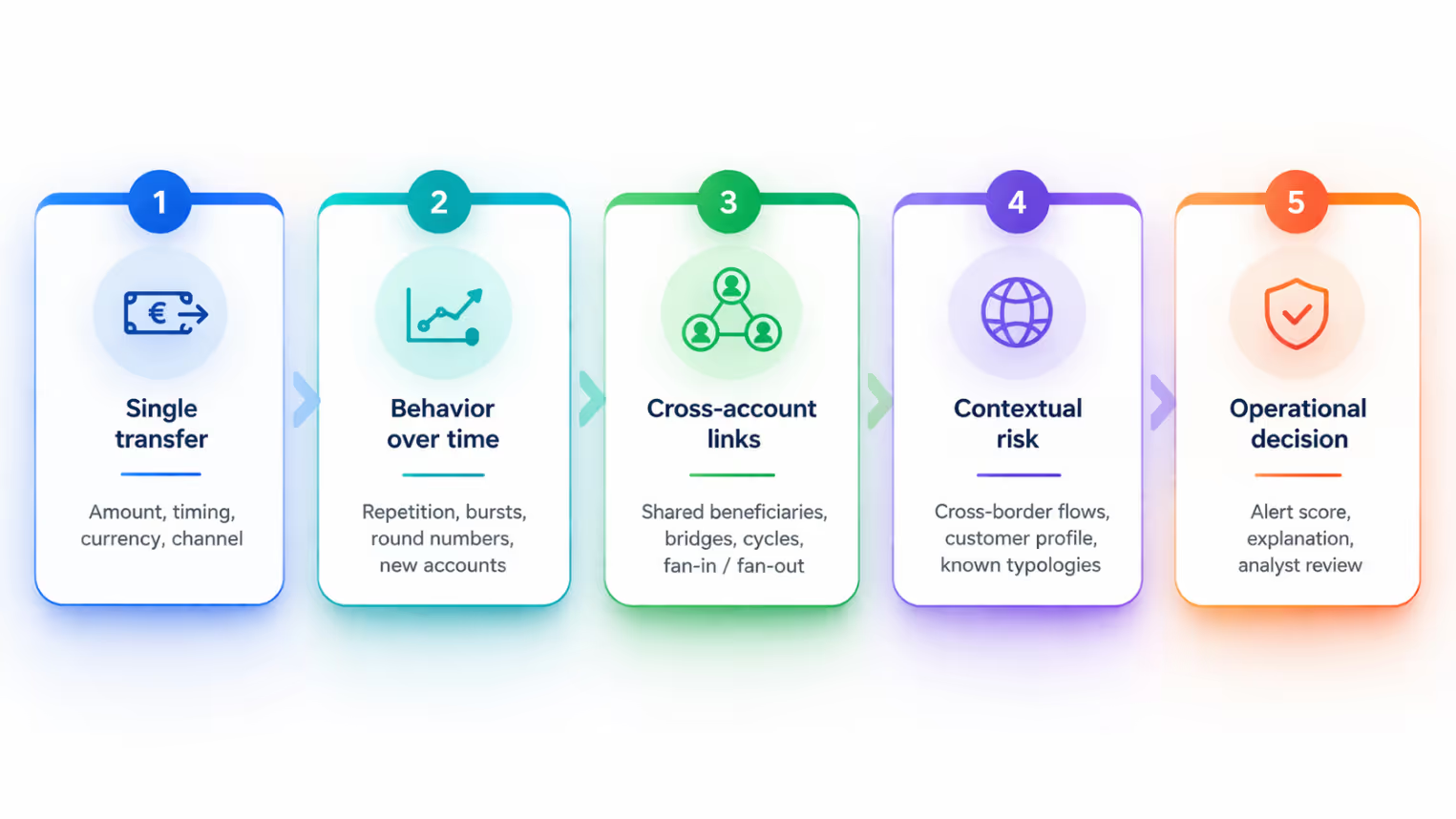
The literature is relatively consistent about the transaction behaviors that repeatedly trigger concern. Rapid fund movement, structuring or smurfing, activity on dormant or newly opened accounts, repetitive round-number transfers, unusual cross-border flows, and circular or multi-hop transaction chains are among the most common typologies highlighted in recent works [10, 15, 18, 21, 27]. Studies on remittances, mobile money, and cross-country transfer networks show that the same suspicious logic often reappears in new channels: what changes is the data environment, not the underlying need to reconstruct intent from fragmented transaction traces [5, 7, 11, 15, 19].
A useful contribution from the broader review literature is that suspicious transaction detection is only one part of the AML technology landscape, but it is the part that has attracted the largest concentration of technical work. The 2019 systematic review by Sobreira Leite and colleagues already observed that suspicious transaction detection dominated the literature, with data mining methods appearing most often among the support mechanisms studied [30]. More recent reviews confirm that the field has since diversified into machine learning, graph networks, and AI-assisted monitoring, while still returning to the same operational pain points: alert overload, class imbalance, sparse labels, and the tension between detection power and explainability [8, 39].
The technical evolution can be read as a shift from isolated transactions to connected behavior. Early systems mainly asked whether a single transfer crossed a threshold. Statistical approaches then asked whether a transaction deviated from peer behavior. Machine learning systems began learning suspicious profiles from historical cases. Graph-based methods moved one step further by treating suspicious activity as a relational process rather than an isolated event. The current frontier combines these views instead of choosing only one [9, 17, 25, 35].
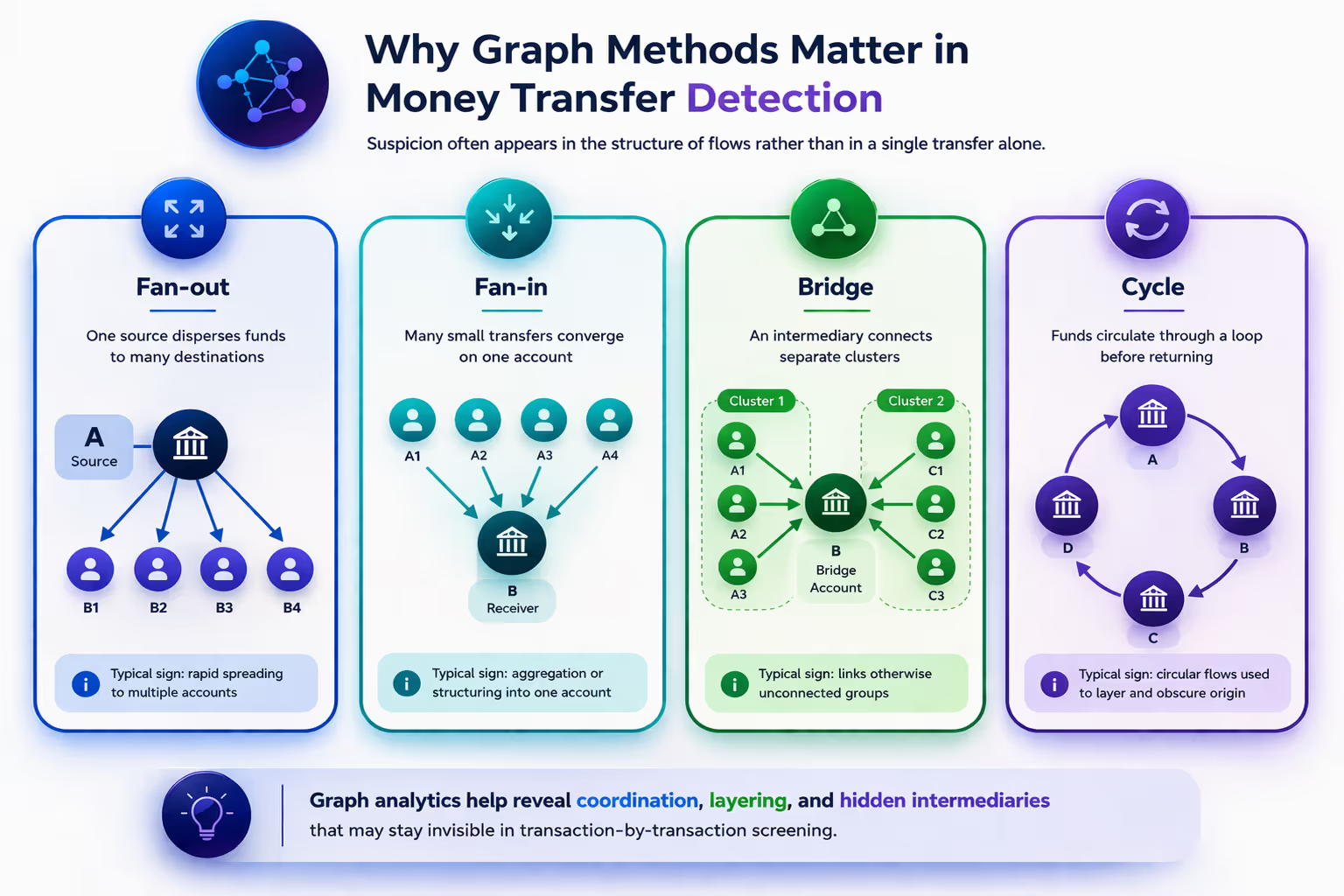
Graph and network perspectives have become central because suspicious activity is structurally relational. Money does not simply move; it is routed, split, recombined, and buffered through entities that may appear innocuous when viewed alone. This is why graph metrics, social network analysis, and graph neural networks have become so important in the literature. Earlier network-based work showed that client risk could be inferred from relational position, mediation roles, and network peripherality [34]. Later studies extended this insight to temporal transfer networks and transaction graphs, showing that cycles, hidden paths, and multi-layered flows can be surfaced more effectively when accounts, transfers, and counterparties are modeled as connected systems rather than rows in a flat table [1, 5, 11, 12, 35, 37].
The recent graph learning literature also suggests a practical division of labor. Hand-crafted graph metrics remain useful for investigative visibility and feature engineering, while heterogeneous GNNs appear promising when institutions have richer entity-level data and enough infrastructure to train on large relational graphs. Studies using real transaction graphs and heterogeneous business-role networks all point in the same direction: graph learning improves the ability to capture suspicious structures that are hard to see with transaction-level classifiers alone [1, 2, 12, 35, 37, 38].
Figure 3 highlights four recurring graph patterns that frequently motivate network-based detection strategies in the literature.
Deep learning has also matured from a vague promise into a more targeted tool. Sequence models and attention-based architectures are especially relevant when suspicious behavior unfolds over time rather than in one event. This matters for money transfer monitoring because laundering patterns often depend on timing, recurrence, and sequencing. Recent work on fund transfer fraud, temporal cross-border detection, and alarm qualification shows that deep learning can be particularly useful for ranking alerts, modeling sequential dependencies, and improving recall in large-scale streams [2, 19, 23, 32, 38].
At the same time, the literature is clear that performance alone is not enough. Compliance teams need to understand why a transaction was flagged, and regulators increasingly expect defensible logic rather than a black-box score. This explains the rise of explainable and hybrid systems. Autoencoder plus risk-based models, criminology-informed frameworks, graph-enhanced alert triage, and explainable graph systems such as xFraud all reflect the same practical idea: institutions want models that do not merely predict risk, but can also support human review, prioritization, and documentation [13, 28, 31, 33, 40].
One of the most persistent themes in the literature is that the hardest part is often not the algorithm but the data regime. Labels are scarce, class imbalance is severe, and genuine suspicious cases are usually reviewed through operational processes that were not designed for machine learning. Several studies therefore focus on feature engineering, resampling, client-level profiling, and alert scoring rather than on end-to-end replacement of existing monitoring systems [3, 10, 24, 26, 29, 36]. In practice, this means the strongest systems are often not the most exotic ones, but the ones that can turn messy banking data into stable, reviewable signals.
This is also why false positives remain the field’s defining operational cost. Rule-heavy systems overwhelm investigators; naive machine learning can improve precision but still fail if the training labels reflect historical review bias; and aggressive alert suppression introduces the danger of hiding true positives. Recent studies on scoring models, XGBoost-based suppression, and graph-assisted alert optimization are valuable precisely because they address this middle layer between raw transaction monitoring and final investigator action [10, 27, 31, 33]. The state of the art is therefore not just better detection, but better alert management.
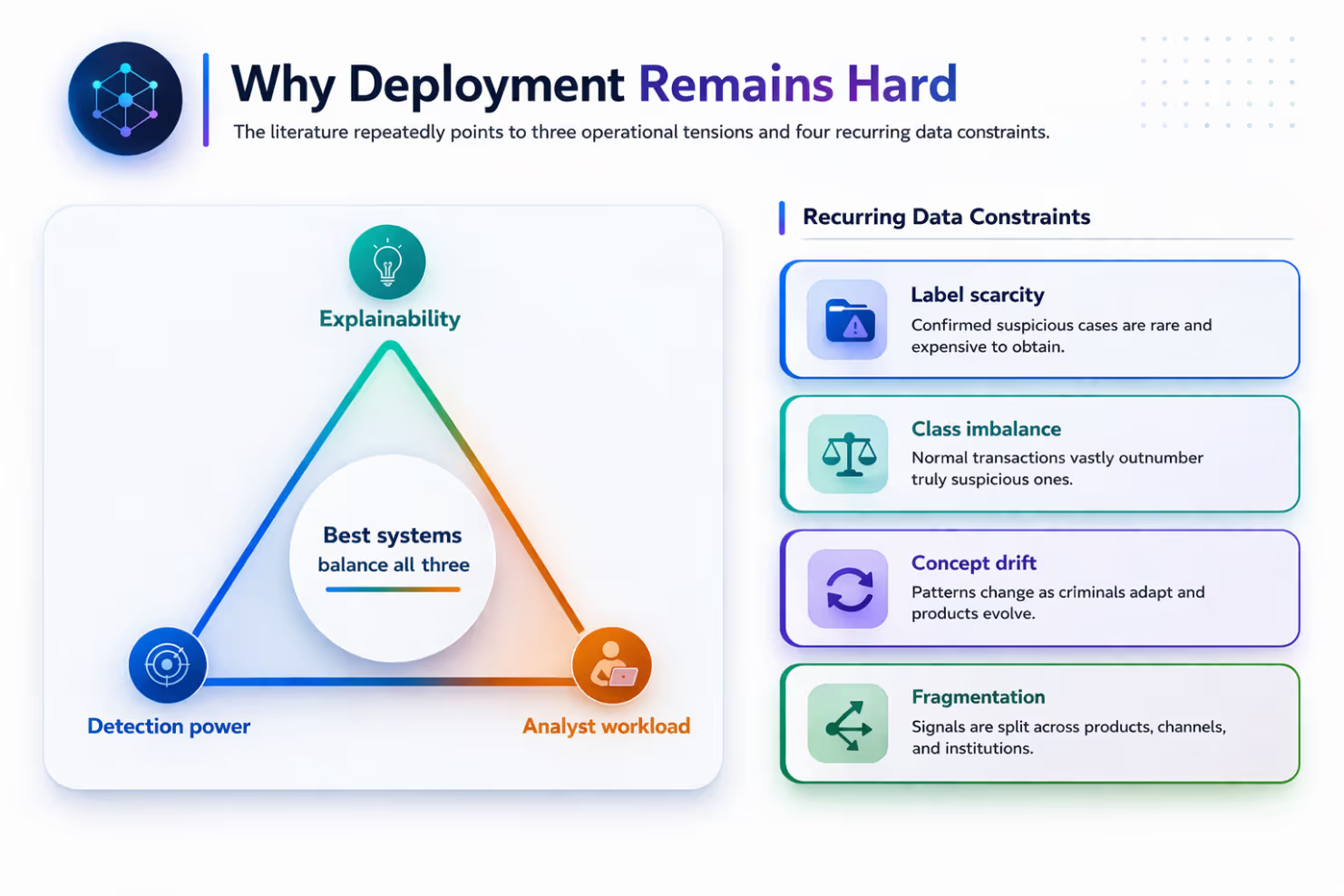
Figure 4 summarizes the operational trade-offs and data constraints that repeatedly shape real-world deployment decisions.
The newer frontier is expansion beyond classic domestic bank transfers. The literature is increasingly attentive to mobile money, migrant remittances, blockchain environments, and cross-institution or cross-border monitoring. In these settings, the technical challenge is not only accuracy but adaptation: models must handle new transaction semantics, shifting fraud behavior, and fragmented oversight across platforms [7, 15, 21]. Research on bitcoin and blockchain transaction graphs, for example, reinforces the value of temporal and structural modeling, but it also shows that AML methods must adapt to ecosystems where entities, addresses, and transaction semantics differ from traditional retail banking [21, 38].
Another frontier is privacy-preserving collaboration. Detection systems often suffer because suspicious behavior spans more than one institution, while the data needed to reconstruct those patterns cannot always be freely shared. Literature has not fully solved this problem, but it increasingly acknowledges it. Broader graph-learning and fraud detection work suggests that scalable distributed architectures, privacy-preserving analytics, and explainable graph systems will matter more as monitoring expands across organizational boundaries [35, 37, 40]. Industry-facing analysis likewise emphasizes that transaction monitoring is no longer only a modeling problem; it is also a systems, governance, and interoperability problem [22].
Taken together, the state of the art can be summarized in four practical lessons. First, rule-based systems are still necessary, but rarely sufficient on their own [17, 22, 30]. Second, machine learning adds the most value when it is used to rank, triage, and contextualize alerts rather than simply replace every existing rule [3, 6, 10, 31, 33]. Third, graph approaches are no longer a niche idea; they are now one of the most convincing technical responses to layering, circular flows, and hidden counterpart relationships [1, 5, 11, 12, 34, 37]. Fourth, explainability is not a cosmetic add-on. It is part of what makes a detection system usable in real institutions [13, 22, 28, 32, 40].
There are still important gaps. The literature remains uneven across geographies and payment ecosystems. High-quality public datasets are limited. Comparative evaluations are often difficult because studies use different labels, objectives, and class distributions. Some papers report strong performance gains, but operational transferability remains harder to judge than laboratory accuracy. For that reason, the most convincing recent reviews call for more realistic evaluation, stronger benchmarking, and a closer connection between technical design and the actual workflow of investigators and compliance teams [8, 22, 30, 39].
Suspicious activity detection in money transfer transactions has evolved from threshold policing into multi-layer financial intelligence. The field now combines transaction features, temporal patterns, graph structure, alert triage, and explainability in ways that were far less mature even a few years ago. The most important insight from the literature is not that one algorithm has won. It is that effective detection systems is increasingly architectural: rules, statistics, machine learning, graph reasoning, and human investigation each solve different parts of the problem.
For a practical reader, the current state of the art points toward hybrid design. Use rules to encode clear policy constraints. Use statistical and ML models to surface deviations and prioritize workload. Use graph methods when laundering behavior is likely to be relational or layered and build explainability into the system from the start, not as an afterthought. That is the direction in which the literature is moving, and it is the direction most likely to make suspicious activity detection both more accurate and more operationally credible.
[1] Karim, M., Hermsen, F., Chala, S., De Perthuis, P., & Mandal, A. (2024). Scalable semi-supervised graph learning techniques for anti money laundering. IEEE Access, 12, 50012-50029. https://doi.org/10.1109/ACCESS.2024.3383784
[2] Shih, Y.-C., Dai, T.-S., Chen, Y.-J., Ti, Y.-W., Wang, W.-T., & Kuo, Y.-H. (2024). Fund transfer fraud detection: Analyzing irregular transactions and customer relationships with self-attention and graph neural networks. Expert Systems with Applications, 259, 125211. https://doi.org/10.1016/j.eswa.2024.125211
[3] Jullum, M., Loland, A., Huseby, R. B., Anonsen, G., & Lorentzen, J. (2020). Detecting money laundering transactions with machine learning. Journal of Money Laundering Control, 23(1), 173-186. https://doi.org/10.1108/JMLC-07-2019-0055
[4] Upadhyay, N., Rathore, Y., Bansal, N., Jhingran, S., Chaudhary, G., Maurya, S., Chaturvedi, R., & Soni, K. (2025). Machine learning perspective: Fraud payment transaction detection. Journal of Mobile Multimedia. https://doi.org/10.13052/jmm1550-4646.213414
[5] Vilella, S., Lupi, A., Fornasiero, M., Moncalvo, D., Ricci, V., Ronchiadin, S., & Ruffo, G. (2023). Anomaly detection in cross-country money transfer temporal networks. arXiv. https://doi.org/10.48550/arXiv.2311.14778
[6] Alexandre, C., & Balsa, J. (2023). Incorporating machine learning and a risk-based strategy in an anti-money laundering multiagent system. Expert Systems with Applications, 217, 119500. https://doi.org/10.1016/j.eswa.2023.119500
[7] Lokanan, M. (2023). Predicting mobile money transaction fraud using machine learning algorithms. Applied AI Letters. https://doi.org/10.1002/ail2.85
[8] Mallika, B. K., & Ramasubramanian, V. H. (2025). Anti money laundering system in detecting and preventing money laundering activities: A systematic review. Journal of Money Laundering Control, 28(2), 385-407. https://doi.org/10.1108/JMLC-07-2024-0108
[9] Jensen, R. I. T., & Iosifidis, A. (2022). Fighting money laundering with statistics and machine learning. IEEE Access, 11, 8889-8903. https://doi.org/10.1109/ACCESS.2023.3239549
[10] Halford, E., Gibson, I., Newfield, M., & Dhanwala, M. (2025). Developing a scoring model for managing money laundering transactions using machine learning. Journal of Money Laundering Control. https://doi.org/10.1108/JMLC-09-2024-0152
[11] Vilella, S., Lupi, A., Ruffo, G., Fornasiero, M., Moncalvo, D., Ricci, V., & Ronchiadin, S. (2023). Exploiting graph metrics to detect anomalies in cross-country money transfer temporal networks. Companion Proceedings of the ACM Web Conference 2023. https://doi.org/10.1145/3543873.3587602
[12] Huong, H., Nguyen, X., Dang, T., & Tran-Truong, P. (2024). Money laundering detection using a transaction-based graph learning approach. 2024 18th International Conference on Ubiquitous Information Management and Communication (IMCOM), 1-8. https://doi.org/10.1109/IMCOM60618.2024.10418307
[13] Koo, K., Park, M., & Yoon, B. (2024). A suspicious financial transaction detection model using autoencoder and risk-based approach. IEEE Access, 12, 68926-68939. https://doi.org/10.1109/ACCESS.2024.3399824
[14] Canhoto, A. I. (2020). Leveraging machine learning in the global fight against money laundering and terrorism financing: An affordances perspective. Journal of Business Research, 131, 441-452. https://doi.org/10.1016/j.jbusres.2020.10.012
[15] Mbiva, S., & Correa, F. (2024). Machine learning to enhance the detection of terrorist financing and suspicious transactions in migrant remittances. Journal of Risk and Financial Management, 17(5), 181. https://doi.org/10.3390/jrfm17050181
[16] Alkhalili, M., Qutqut, M. H., & Almasalha, F. (2021). Investigation of applying machine learning for watch-list filtering in anti-money laundering. IEEE Access, 9, 18481-18496. https://doi.org/10.1109/ACCESS.2021.3052313
[17] Chen, Z., Van Khoa, L., Teoh, E. N., Nazir, A., Karuppiah, E. K., & Lam, K. P. (2018). Machine learning techniques for anti-money laundering (AML) solutions in suspicious transaction detection: A review. Knowledge and Information Systems, 57, 245-285. https://doi.org/10.1007/s10115-017-1144-z
[18] Ketenci, U., Kurt, T., Onal, S., Erbil, C., Akturkoglu, S., & Ilhan, H. (2021). A time-frequency based suspicious activity detection for anti-money laundering. IEEE Access, 9, 59957-59967. https://doi.org/10.1109/ACCESS.2021.3072114
[19] Yu, Q., Xu, Z., & Ke, Z. (2024). Deep learning for cross-border transaction anomaly detection in anti-money laundering systems. 2024 6th International Conference on Machine Learning, Big Data and Business Intelligence (MLBDBI), 244-248. https://doi.org/10.1109/MLBDBI63974.2024.10823769
[20] Nama, F., & Obaid, A. (2024). Financial fraud identification using deep learning techniques. Al-Salam Journal for Engineering and Technology. https://doi.org/10.55145/AJEST.2024.03.01.012
[21] Oad, A., Razaque, A., Tolemyssov, A., Alotaibi, M., Alotaibi, B., & Zhao, C. (2021). Blockchain-enabled transaction scanning method for money laundering detection. Electronics. https://doi.org/10.20944/preprints202106.0172.v1
[22] Oztas, B., Cetinkaya, D., Adedoyin, F., Budka, M., Aksu, G., & Dogan, H. (2024). Transaction monitoring in anti-money laundering: A qualitative analysis and points of view from industry. Future Generation Computer Systems, 159, 161-171. https://doi.org/10.1016/j.future.2024.05.027
[23] Bi, W., Trinh, T., & Fan, S. (2024). Machine learning-based pattern recognition for anti-money laundering in banking systems. Journal of Advanced Computing Systems. https://doi.org/10.69987/JACS.2024.41103
[24] Reite, E., Karlsen, J., & Westgaard, E. (2024). Improving client risk classification with machine learning to increase anti-money laundering detection efficiency. Journal of Money Laundering Control. https://doi.org/10.1108/JMLC-03-2024-0040
[25] Zhang, Y., & Trubey, P. (2018). Machine learning and sampling scheme: An empirical study of money laundering detection. Computational Economics, 54, 1043-1063. https://doi.org/10.1007/s10614-018-9864-z
[26] Hsin, Y., Dai, T., Ti, Y., Huang, M., Chiang, T., & Liu, L. (2022). Feature engineering and resampling strategies for fund transfer fraud with limited transaction data and a time-inhomogeneous modi operandi. IEEE Access, 10, 86101-86116. https://doi.org/10.1109/ACCESS.2022.3199425
[27] De Oliveira, J., & Leal, A. (2024). Enhancing anti-money laundering protocols: Employing machine learning to minimise false positives and improve operational cost efficiency. Proceedings of the 2024 8th International Conference on Advances in Artificial Intelligence. https://doi.org/10.1145/3704137.3704156
[28] Ramadhan, S. (2024). Harnessing machine learning for money laundering detection: A criminological theory-centric approach. Journal of Money Laundering Control. https://doi.org/10.1108/JMLC-04-2024-0083
[29] Ti, Y., Hsin, Y., Dai, T., Huang, M., & Liu, L. (2022). Feature generation and contribution comparison for electronic fraud detection. Scientific Reports, 12. https://doi.org/10.1038/s41598-022-22130-2
[30] Sobreira Leite, G., Albuquerque, A. B., & Pinheiro, P. R. (2019). Application of technological solutions in the fight against money laundering - A systematic literature review. Applied Sciences, 9(22), 4800. https://doi.org/10.3390/app9224800
[31] Bakry, A. N., Alsharkawy, A. S., Farag, M. S., & Raslan, K. R. (2024). Automatic suppression of false positive alerts in anti-money laundering systems using machine learning. The Journal of Supercomputing, 80, 6264-6284. https://doi.org/10.1007/s11227-023-05708-z
[32] Jensen, R. I. T., & Iosifidis, A. (2023). Qualifying and raising anti-money laundering alarms with deep learning. Expert Systems with Applications, 214, 119037. https://doi.org/10.1016/j.eswa.2022.119037
[33] Naser Eddin, A., Bono, J., Aparicio, D., Polido, D., Ascensao, J. T., Bizarro, P., & Ribeiro, P. (2021). Anti-money laundering alert optimization using machine learning with graphs. arXiv. https://doi.org/10.48550/arXiv.2112.07508
[34] Fronzetti Colladon, A., & Remondi, E. (2017). Using social network analysis to prevent money laundering. Expert Systems with Applications, 67, 49-58. https://doi.org/10.1016/j.eswa.2016.09.029
[35] Weber, M., Chen, J., Suzumura, T., Pareja, A., Ma, T., Kanezashi, H., Kaler, T., Leiserson, C. E., & Schardl, T. B. (2018). Scalable graph learning for anti-money laundering: A first look. arXiv. https://doi.org/10.48550/arXiv.1812.00076
[36] Harris, D. A., Pyndiura, K. L., Sturrock, S. L., & Christensen, R. A. G. (2021). Using real-world transaction data to identify money laundering: Leveraging traditional regression and machine learning techniques. STEM Fellowship Journal, 7(1), 21-32. https://doi.org/10.17975/SFJ-2021-006
[37] Johannessen, F., Yurchenko, V., Meling, H., Frid-Nielsen, S., & Stokke, O. M. (2025). Finding money launderers using heterogeneous graph neural networks. Journal of Finance and Data Science, 11, 100175. https://doi.org/10.1016/j.jfds.2025.100175
[38] Wan, F., & Li, P. (2024). A novel money laundering prediction model based on a dynamic graph convolutional neural network and long short-term memory. Symmetry, 16(3), 378. https://doi.org/10.3390/sym16030378
[39] Mousavian, S., & Miah, S. J. (2025). Review of artificial intelligence-based applications for money laundering detection. Intelligent Systems with Applications, 27, 200572. https://doi.org/10.1016/j.iswa.2025.200572
[40] Rao, S. X., Zhang, S., Han, Z., Zhang, Z., Min, W., Chen, Z., Shan, Y., Zhao, Y., & Zhang, C. (2022). xFraud: Explainable fraud transaction detection. Proceedings of the VLDB Endowment, 15(3), 427-436. https://doi.org/10.14778/3494124.3494128
© Thinsaction 2026 — No part of this article may be reproduced without attribution.