How Child Exploitation Hides in Plain Sight Inside Remittance Networks


Each transfer is one euro. Sometimes two. They leave the same account, in rapid succession, over one month. They arrive at dozens of different recipients — accounts that share no visible relationship, in some cases across borders.
These payments have been documented, in regulatory reports by FATF, FinTRAC, and AUSTRAC, as being used to purchase access to child sexual abuse material — videos, photographs, and live-streamed sessions directed in real time by the sender.
This is not a hypothetical. According to FATF's 2024 report on the online sexual exploitation of children, this is the documented payment typology for a specific and growing category of financial crime — one that flows predominantly through mobile money networks and remittance platforms, not banks. FinTRAC updated its operational guidance in 2025 to reflect a measurable increase in this pattern. AUSTRAC has made it a dedicated category for suspicious matter reporting.
The infrastructure exists. The payments are happening. What is largely absent is the capacity to detect them automatically, at scale, inside the transaction data that operators already hold.
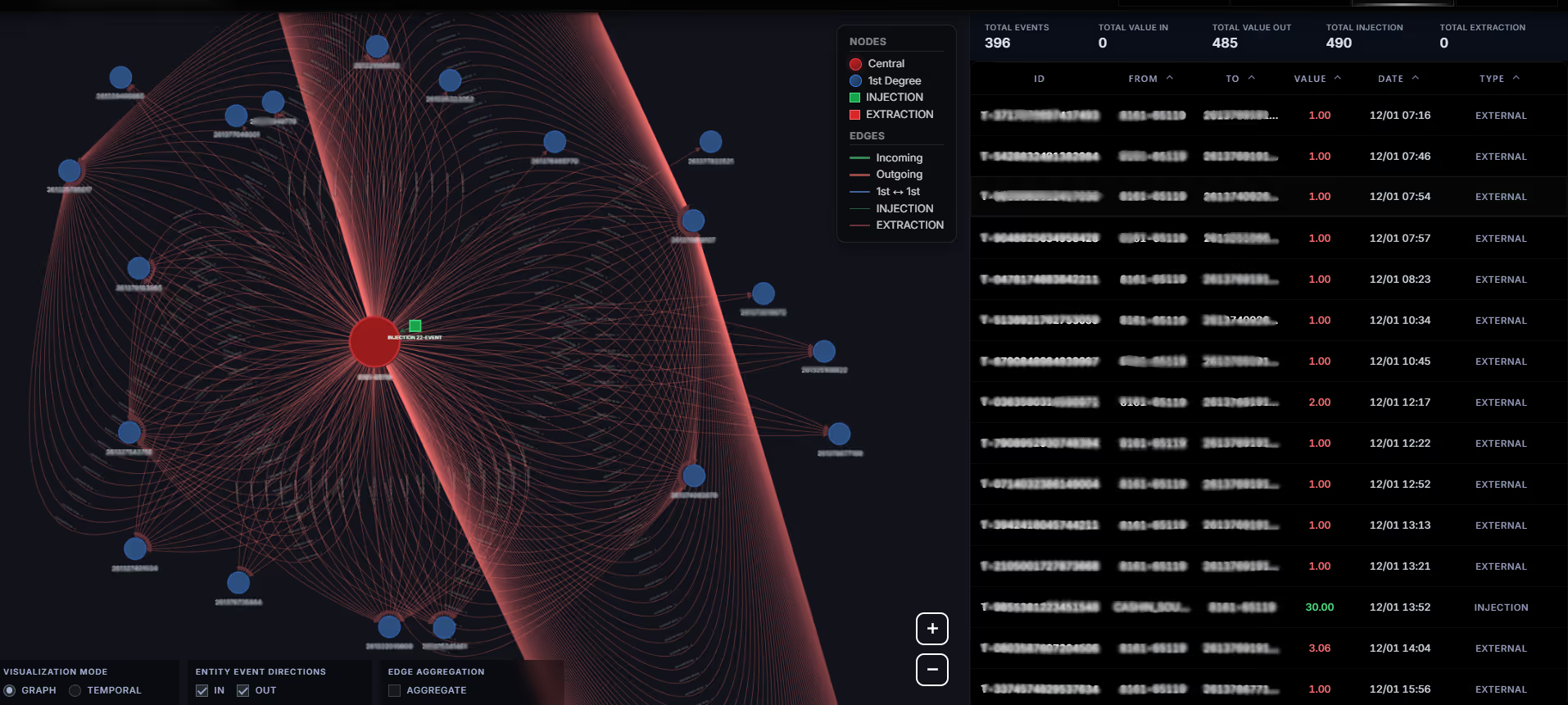
The graph above shows one account, observed over a few days. It sent 396 transactions. Median value: €1.00. Total outbound volume: €485. Its own peer-to-peer inbound balance: zero — all liquidity came from multiple cash-in operations.
This account is not a collector. It is a distributor. It receives funds from outside the network, then immediately disperses them outward in micro-amounts to a large number of distinct recipients.
This pattern — a central node that loads funds via cash-in and fans out into dozens of low-value transfers — is what we call a Coordinated Micro-Transfer Pattern (CMTP). It has a specific network topology, a specific temporal signature, and a specific combination of measurable features that distinguish it from legitimate high-volume activity.
Traditional AML systems do not detect it. Not because the data isn't there — it is. Because these systems were not designed to see structure. They were designed to see transactions.
The crime is not in the transaction. It is in the structure.

Rule-based compliance infrastructure operates on a simple logic: define thresholds, monitor for breaches, flag deviations from known patterns. This was built for a different threat model — large sums, few accounts, clear directionality.
It fails here for four specific reasons.
Amounts are sub-threshold by design
One euro is not a suspicious transaction. Neither is two euros. The offense is not located in any individual payment. It is located in the aggregate behavior of hundreds of payments from one account to many recipients, in a compressed time window. Rules evaluate rows. This pattern lives in the shape of the data.
Individual transaction analysis misses topology
A compliance officer reviewing a log sees a list. The same data, rendered as a graph, shows a star: one central node with dozens of outbound edges, funded by cash-in operation, sending uniform micro-amounts in rapid succession. That shape is immediately anomalous. In tabular form, it is invisible.
Static snapshots miss behavioral transitions
The accounts involved in this pattern do not behave consistently over time. They exhibit statistical changepoints — moments where the properties of the transaction time series shift abruptly. Before the cash-in: near-dormant. After: high-frequency outbound activity within minutes. This transition is a behavioral signature. It does not appear in any static compliance report.
Identity-centric models miss flow-centric patterns
The question "does this person look suspicious?" is less powerful than the question "does this structure look suspicious?" The latter is harder to evade, more consistent across jurisdictions, and detectable without requiring identity information.
Before describing the detection approach, a clarification is necessary — because the data reveals not one pattern but two complementary structures that often appear together in the same transaction network.
The first is the distribution node
The account holder performs a cash-in, then immediately fans out micro-transfers toward many recipients. It is the buyer — or the intermediary acting on behalf of buyers.
The second is the collection node
An account that receives micro-transfers from many sources and accumulates them without redistribution. It is the recipient infrastructure — an account held by a facilitator, collecting payments from multiple buyers before a single cash-out event.
Both structures are anomalous. Both are detectable through graph analysis. Both appear in the documented typology for CSAE financing. An effective detection system must identify both — and recognize when they exist in proximity within the same transaction network.

The account above was observed over approximately one month. Its behavior was not constant.
Funds loaded by the account holder before redistribution. What follows each cash-in , within hours, is a cascade of outbound micro-transfers.
The elapsed time between cash-in and first outbound transfer is measured in minutes. The number of transfers that follow is inconsistent with any normal pattern of personal expenditure.
Detecting this requires analyzing not what an account looks like at a point in time, but how and when its behavior changes. Changepoint detection applied to mobile money transaction streams surfaces this transition automatically, at scale, across millions of accounts — returning the specific subset that combines the structural topology described above with the behavioral shift visible in the temporal view.
Money service businesses are subject to FATF Recommendation 16, which mandates transaction monitoring proportionate to documented risk typologies. Low-value high-frequency transfers exhibiting the CMTP signature fall within the specific guidance issued by FATF, FinTRAC, and AUSTRAC in relation to CSAE financing.
Meeting this obligation requires the capacity to answer five questions about any account in the network:
These are not questions that rule-based systems, as currently deployed in most MSB compliance infrastructure, are designed to answer. They require graph-based structural analysis, temporal changepoint detection, and multi-feature behavioral profiling — applied continuously, at scale, across the full transaction graph.
The patterns described in this article are not theoretical. They are present — documented, measurable, and structurally distinct — inside mobile money transaction data. The analytical methods to detect them exist. The regulatory obligation to act on them is unambiguous.
What remains is an infrastructure gap: the distance between what compliance systems were built to find and what the data, properly analyzed, actually reveals.
The question is not whether these patterns exist in your network today. The question is whether anyone is looking.
References:
© Thinsaction 2026 — No part of this article may be reproduced without attribution.