Money Mule Accounts: From Recruitment to Detection


Financial crime does not fail because criminals are careless. It fails because the systems it builds leave structural residue.
A money mule account is not a strange or exceptional artifact. It is a functional component of criminal infrastructure—predictable in its role, reproducible in its design, and detectable in its shape. Understanding it requires less focus on individual suspicious transactions and more focus on what the account does within its network.
This article examines money mule accounts across three levels of analysis: the human layer of recruitment and motivation, the operational mechanics of how mule networks function, and the structural and temporal signatures that make them detectable even when no individual transaction appears abnormal.
A money mule is an individual whose bank account—knowingly or not—receives, holds, and forwards criminal proceeds on behalf of a criminal operator. The term reflects the operational role: the account carries value across the financial system, placing distance between the crime and its beneficiary.
This distance serves two purposes:
FinCEN's 2019 Advisory on Money Mule Schemes describes mule activity as a foundational mechanism in the laundering of proceeds from elder fraud, business email compromise, romance scams, and tax refund fraud—a consistent presence across the fraud typology landscape.
Mule accounts do not self-assemble. Criminal networks build them through deliberate, scalable recruitment operations. The common thread across all recruitment methods is plausible deniability: the recruited individual should believe—or be able to claim—that their activity is legitimate.

The operational implication is significant: professional mules introduce coordination above the individual account level. Detection at the single-account level will systematically underperform when mule networks include a professional management layer.
A mule account follows a predictable operational workflow, regardless of the fraud typology it serves:
Three behavioral characteristics are consistent across all mule account typologies:
This is not random behavior. It is operational logic: aggregate from many, concentrate toward one.
The central analytical insight is this: a mule account's function creates its structure. The criminal purpose of the account—gather widely, transit quickly, disperse narrowly—produces a geometric shape in the transaction graph that is identifiable independent of amounts, flags, or account metadata.
That shape is the gather-scatter pattern.
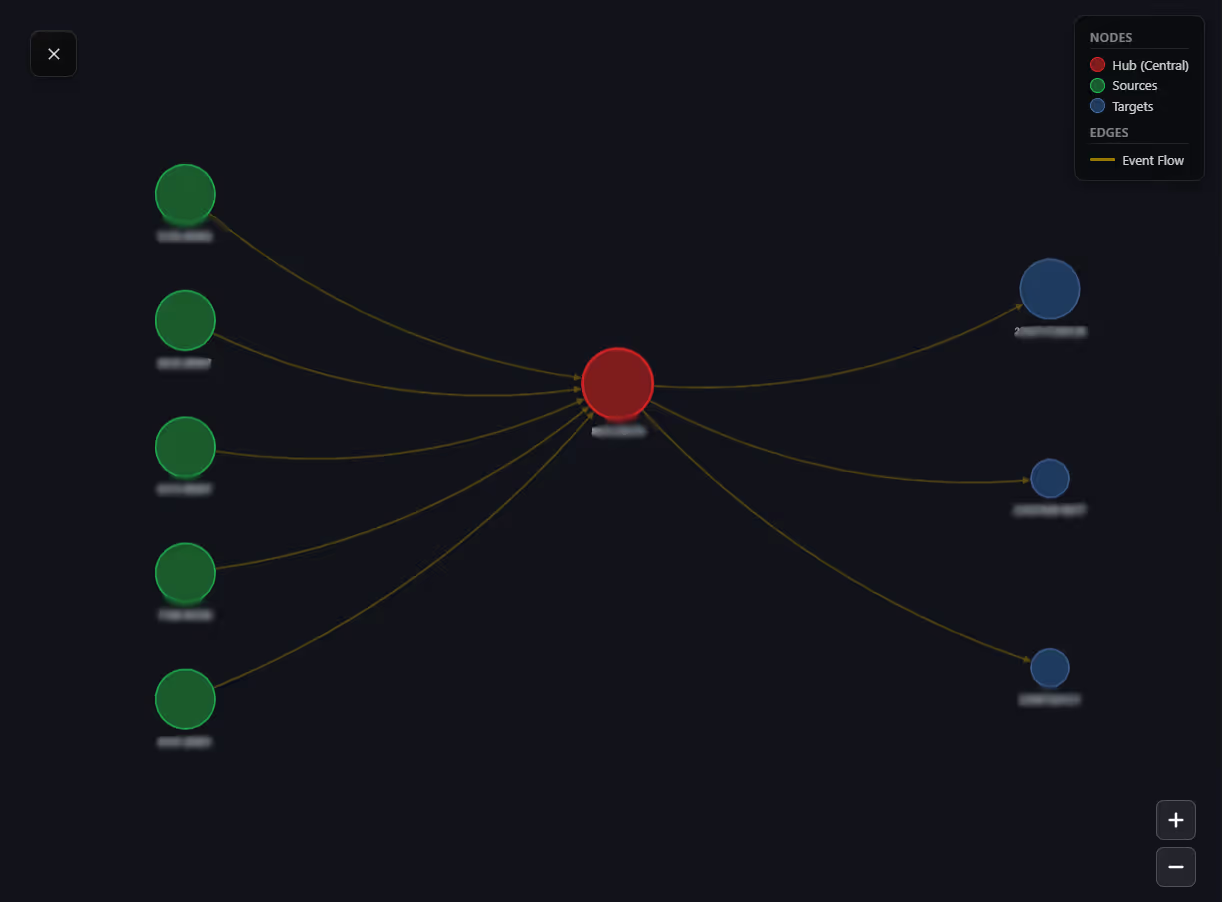
Multiple accounts send funds to the mule within a defined time window. Analytically, these incoming sources are:
This is the fingerprint of coordinated sourcing at scale. Legitimate accounts do receive from multiple senders—but legitimate sources tend to be recurring, geographically consistent, and temporally predictable. The mule pattern diverges on all three dimensions.
Following the gather, the hub redirects funds outward—rapidly and toward a concentrated set of destinations. The temporal interval between incoming and outgoing transactions is characteristically short. The account is not accumulating value; it is channeling it.
The combination—many inbound, few outbound, compressed time window—is the structural definition of mule behavior in a transaction graph. Structure reveals what amounts cannot.
Individual mule accounts are rarely deployed in isolation. Criminal networks coordinate multiple mules simultaneously to increase throughput, reduce per-account exposure, and introduce redundancy.
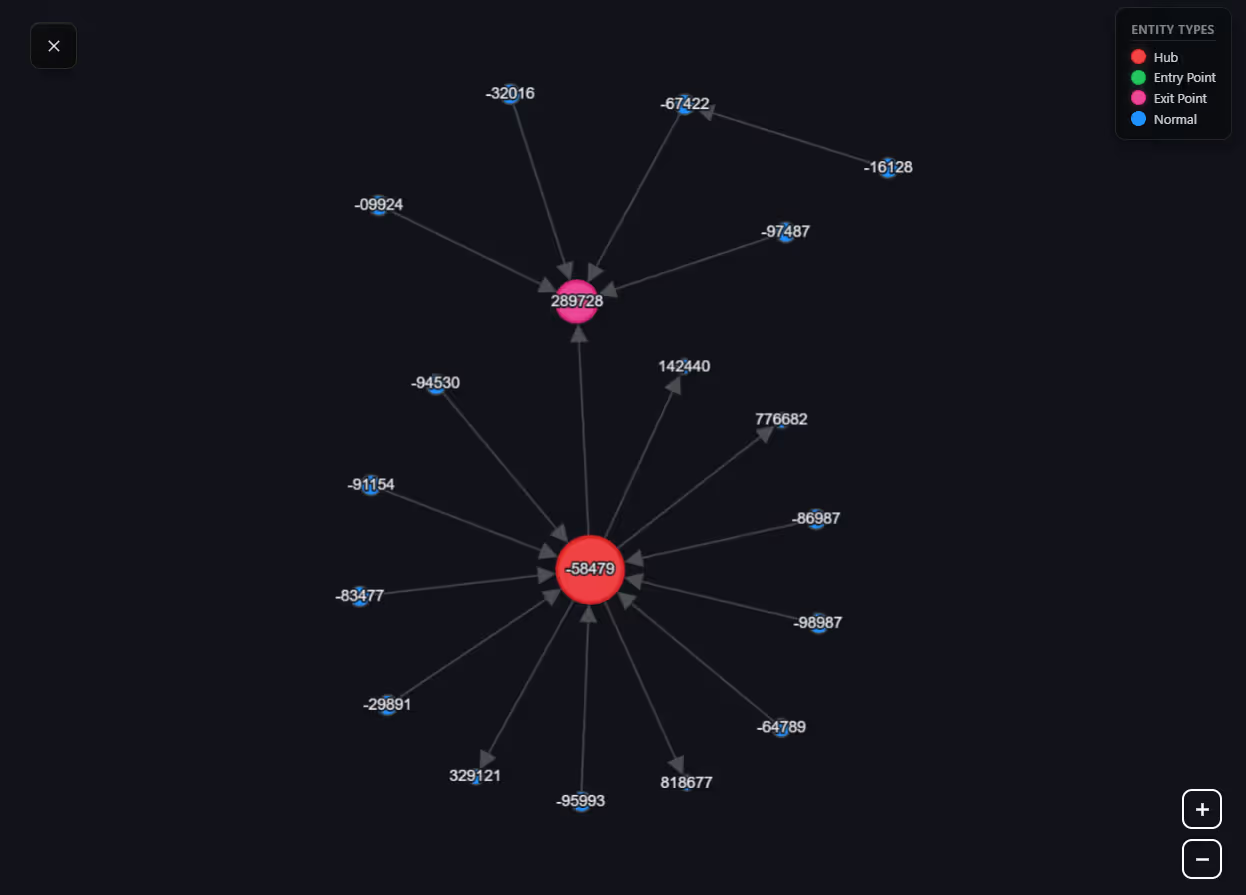
When multiple mule accounts operate in the same network, two structural properties become visible at the graph level:
These network-level properties are invisible when accounts are analyzed individually. They emerge only when the graph is examined as a whole.
A distinguishing characteristic of money mule accounts is their behavioral discontinuity. The transition from ordinary account behavior to mule operation is discrete, not gradual. It marks the moment of recruitment and activation.
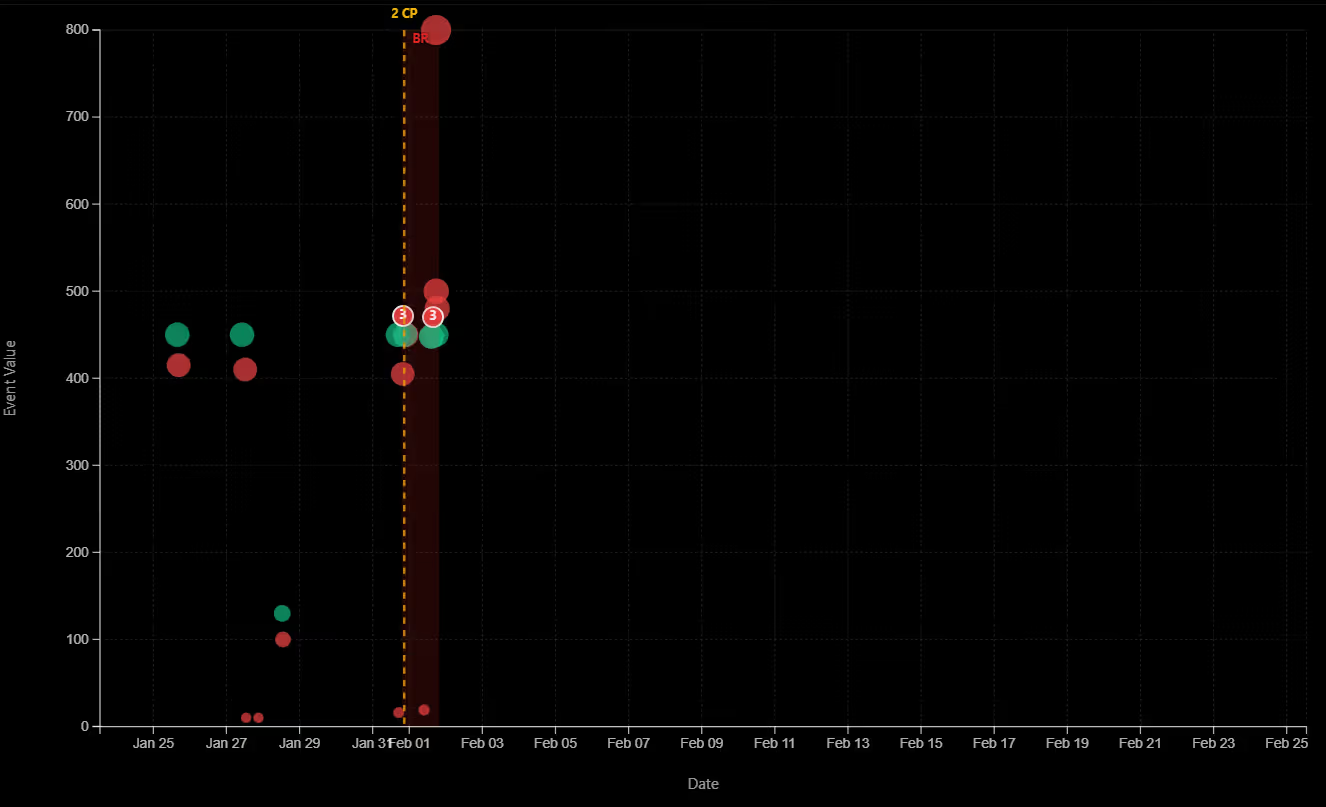
Before activation, the account exhibits typical behavior—or no behavior at all in the case of newly opened accounts. After activation, a structural shift occurs simultaneously across several dimensions:
After the operational window closes, the profile reverts to dormancy. The change is reversible. The record is not.
In coordinated mule networks, this behavioral change point often occurs across multiple accounts within a narrow time window—reflecting the synchronized deployment of a mule cohort. That synchronization amplifies the network-level signal.
Combined with the gather-scatter topology and the community coordination pattern, the temporal signal creates a multi-dimensional convergence. Accounts exhibiting all three simultaneously—structural shape, community membership, and behavioral change point—produce a significantly more robust detection signal than any single dimension in isolation.
Money mule accounts are infrastructure. They are not accidents or anomalies. They are designed components of a system that requires physical and financial distance between criminal operations and criminal proceeds.
That design is their weakness.
The function of a mule account—receive from many, transit quickly, forward to few—produces a structural shape that persists across every variation of the pattern. The shape survives changes in amounts, changes in geography, changes in the underlying fraud typology. It is not contingent on a flagged account or a suspicious amount. It is the geometric consequence of what the account is built to do.
Seeing that shape, understanding it as a role within a coordinated network, and situating it within a behavioral timeline—that is the analytical shift that makes mule detection tractable at scale.
The infrastructure leaves a record. The question is whether you are looking at the right level to read it.
1. Financial Crimes Enforcement Network (FinCEN). Advisory on Imposter Scams and Money Mule Schemes Related to the Coronavirus Disease 2019 (COVID-19) Pandemic. FIN-2019-A005, October 2019.
2. Financial Crimes Enforcement Network (FinCEN). Update on U.S. Currency Restrictions in Mexico: Funnel Accounts and TBML. FIN-2014-A005, May 2014.
3. Europol. European Money Mule Action (EMMA 7) — Results. Joint operation coordinated by Europol and Eurojust, 2022.
4. Financial Action Task Force (FATF). Professional Money Laundering. July 2018.
5. Federal Bureau of Investigation, Internet Crime Complaint Center (IC3). 2023 Internet Crime Report. 2024.
6. Starnini, M., Saracco, F., Yepes, A.J., Peralta, A.F., Tessone, C.J., & Toral, R. (2021). "Smurf-based anti-money laundering in time-evolving transaction networks." PLOS ONE, 16(6).
7. van Vlasselaer, V., Bravo, C., Caelen, O., Eliassi-Rad, T., Akoglu, L., Snoeck, M., & Baesens, B. (2015). "APATE: A novel approach for automated credit card transaction fraud detection using network-based extensions." Decision Support Systems, 75, 38–48.
8. Rakhmetulayeva, S., Duisebekova, K., Buribayev, Z., Bugubayeva, A., Tokmurzina, A., Zhumazhanov, B., & Moldagaliyev, A. (2025). "A Machine Learning Approach for Transaction-Based Money Laundering Detection." Procedia Computer Science, 254, 256–263.