The Transformation Chain: One Pattern, Two Crimes


Money transfer operators and mobile money platforms process millions of low-value transactions daily. Their core function, receiving value from one party and delivering it to another, is legitimate by design. That same function is what makes them structurally attractive to two distinct categories of financial crime. The first category needs to convert physical criminal proceeds into traceable digital funds. The second needs to destroy the digital traceability of stolen funds by extracting them as cash. Both use the same architecture. Both are invisible to conventional monitoring. The pattern is called the transformation chain.
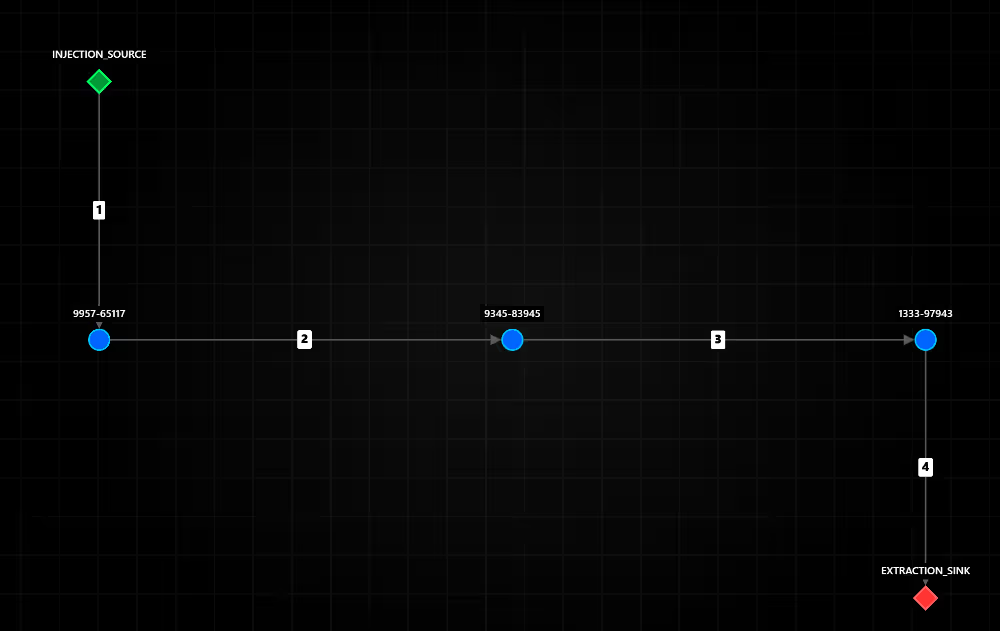
A transformation chain is a bounded sequential path with three distinct components. The first is an injection event, a cash-in transaction through which value enters the network from an external source, whether a cash deposit at a branch, an agent location, or an electronic funding event. The second is a P2P relay chain, a sequence of peer-to-peer transfers between intermediate accounts within the network, each one moving value one step forward without accumulation. The third is an extraction event, a cash-out transaction through which value leaves the network, either as physical cash at a point of service or as a wire transfer to an external bank account.
What defines the pattern is not the number of hops, the amounts, or the identity of the accounts. What defines it is the ordered combination of typed boundary events enclosing a relay chain: the sequence begins with an injection, proceeds through intermediaries, and terminates with an extraction. The value does not stop. It does not accumulate. It transits.
The transformation chain does not exploit a vulnerability in money transfer infrastructure. It exploits its normal function. Cash-in and cash-out are the two most ordinary operations an MTO or mobile money operator processes. A P2P transfer between two users requires no commercial justification, no invoice, and no counterpart documentation. The three transaction types that constitute the transformation chain are, taken individually, the least suspicious events in the operator's daily transaction volume.
This creates a structural gap between what each individual event signals and what the sequence reveals. The gap is not accidental. It is the operational logic of the pattern.
The critical observation is that a monitoring system evaluating transactions individually will see three unremarkable events. A system evaluating the sequence will see a complete layering cycle.
The transformation chain is used by two distinct criminal populations for opposite purposes. What separates them is the direction of the conversion between the injection event and the extraction event, the modal direction of the chain.
The AML case: converting physical criminal proceeds into digital funds
In the money laundering use case, the injection event is a physical cash deposit. The extraction event is a bank wire transfer or digital disbursement. The direction is cash-to-digital.
The operational logic is straightforward. Criminal proceeds in physical cash form, generated by drug trafficking, human smuggling, tax fraud, undeclared labor, or other predicate offences, cannot be spent, invested, or transferred internationally without first acquiring a digital form. Physical cash is inert at scale. It carries no transaction history, but it also cannot be wired, it cannot purchase financial instruments, and it accumulates storage and logistics risk.
The transformation chain solves this. Cash is deposited at an agent or branch, crossing the threshold from the physical economy into the digital network. The P2P relay chain creates temporal and relational distance between the deposit and the final outflow. The wire transfer at the end carries the appearance of a legitimate electronic payment, it has a sender, a timestamp, and a reference number. The funds have been placed and layered within a single bounded operation.
What the criminal acquires is a digital origin story for money that had none.
The fraud case: extracting digital fraud proceeds into untraceable cash
In the fraud use case, the injection event is an electronic funding, a card payment, an incoming wire, or a peer transfer originating from a fraud victim. The extraction event is a physical cash withdrawal at a branch or agent. The direction is digital-to-cash.
The operational logic is the inverse. Fraud proceeds are inherently digital. A compromised card payment, an authorized push payment fraud, a business email compromise disbursement, or the proceeds of a romance scam all arrive as traceable electronic transactions. They carry the fingerprint of the victim: the originating account, the transaction reference, the timestamp, the amount. That fingerprint is the primary evidence in any fraud recovery attempt.
The transformation chain dissolves it. Electronic funds enter the network as a cash-in. The P2P relay chain moves them across accounts, creating distance from the victim's transaction. The cash withdrawal at the end converts them into an untraceable physical form. Once the cash leaves the counter, the digital trail ends. The victim's bank can freeze the sender account. It cannot recover funds that no longer exist as an electronic balance.
What the criminal acquires is physical anonymity for money that was fully traceable.
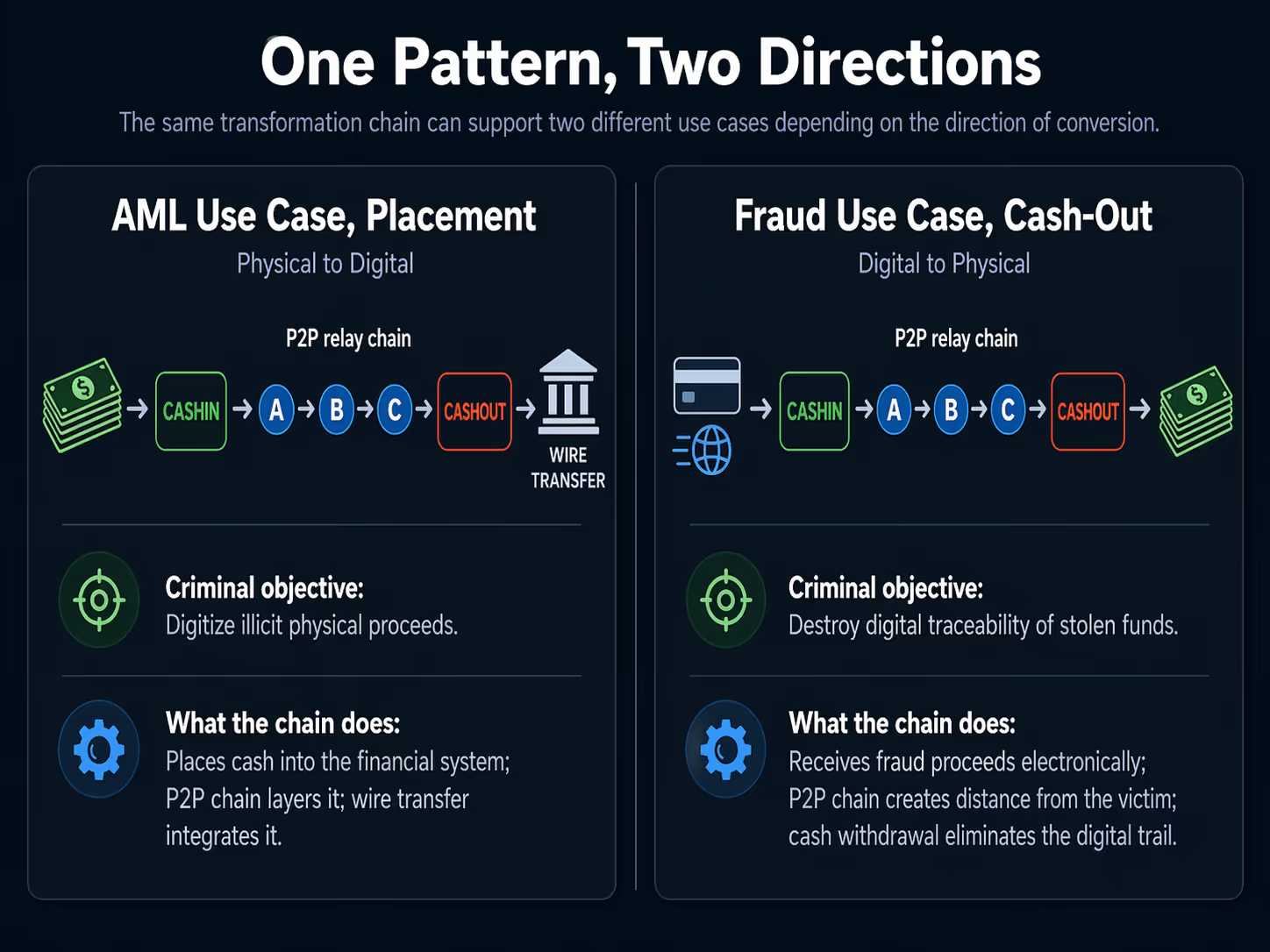
The modal direction of the transformation chain is not a secondary attribute. It is the first piece of information that tells an analyst, a MLRO, or an investigator which crime they are dealing with, which upstream actors to look for, and which downstream recovery actions are available.
The practical consequence is significant. Two alerts from the same detection system, both identifying a CASHIN-P2P-CASHOUT sequence, may require entirely different investigation workflows depending on the modal direction. A compliance team that does not capture this distinction will route both cases through a generic AML investigation process, losing the speed required to initiate fraud recovery before funds are withdrawn, and losing the evidentiary framework required to build a placement case.
Across both use cases, one signal is consistent: temporal compression. The transformation chain is fast. This is not incidental. It is an operational requirement.
In the AML case, speed limits exposure. A cash deposit sitting in an account for several days accumulates behavioral history, triggers velocity rules, and creates a reviewable dwell period. Moving through the chain within hours reduces each of these risks.
In the fraud case, speed is a race against recovery. Fraud victims and their banks typically initiate recovery within hours of recognizing an unauthorized transaction. Every minute between the fraud event and the physical cash withdrawal is a minute in which the funds remain recoverable. The chain compresses that window deliberately.
The empirical result is a pattern where a complete CASHIN-to-CASHOUT cycle, injection through two or three intermediate accounts and then extraction, completes within a window of minutes to a few hours. The sequence documented below completed in 29 minutes across four events.

The transformation chain occupies a specific position in the typology landscape. It is related to several known patterns but is not reducible to any of them.
Smurfing, as characterized by Starnini et al. (2021) and formalized by Shadrooh and Norvag (2024), involves the fragmentation of a large amount into multiple small transactions distributed across several accounts, a scatter-gather or gather-scatter topology. The transformation chain does not fragment. It chains. A single injection point, a sequential relay, a single extraction point. The amount travels intact or with minor decay. There is no many-to-one or one-to-many fan structure.
The daisy chain, as described in the broader layering literature, is a relay sequence through a series of accounts with no typed boundary events. Any account can be an origin and any account can be a destination. The transformation chain is more constrained: the first event must be a CASHIN, the last event must be a CASHOUT. These typed boundaries are not incidental; they are the defining characteristic that gives the pattern its criminal function in the MTO context.
The funnel account pattern, documented by FinCEN (2014) and FATF, describes the convergence of multiple sources into a single account followed by onward movement. That is a many-to-one topology. The transformation chain is one-to-one-to-one-to-one: a single directed path with no convergence layer.
The standard monitoring architecture deployed by most money transfer operators is built around transaction-level rules: thresholds on individual amounts, frequency counters over fixed windows, watchlist screening, and structuring detection based on cumulative cash below reporting limits.
Each of these mechanisms evaluates a transaction or an account in isolation. None of them evaluates a path.
The transformation chain does not cross any individual threshold because it is not designed around individual thresholds. The CASHIN amount is ordinary. The P2P transfers are ordinary. The CASHOUT amount is ordinary. No single event in the sequence triggers a rule. The pattern only becomes visible when the three events are read as a connected sequence, when the system asks not 'is this transaction suspicious?' but 'does this transaction form part of a suspicious sequence that began with a specific event type and terminates with another?'
That is a path query, not a threshold query. Rule-based monitoring systems are not designed to execute path queries across transaction types. They process rows. The transformation chain lives in the relationship between rows, specifically in the ordered relationship between typed rows within a bounded time window.
This is not a calibration failure. It is an architectural mismatch between what the monitoring system was designed to find and what the pattern requires to be found.
Detecting the transformation chain requires three capabilities that are absent from conventional rule-based monitoring and only partially present in standard anomaly detection systems.
The first is a typed transaction graph. Transactions must be represented as directed edges in a graph where the edge type, CASHIN, P2P, or CASHOUT, is a first-class property, not a secondary attribute. Without edge typing, a CASHIN and a P2P transfer are indistinguishable graph edges, and the boundary constraints that define the pattern cannot be enforced.
The second is path extraction with temporal constraints. The system must search the typed graph for directed paths that begin with a CASHIN edge, traverse one or more P2P edges, and terminate with a CASHOUT edge, with all events falling within a defined time window. This is a subgraph query problem over a temporal multigraph. Tariq and Hassani (2023) demonstrated this class of detection at billion-scale transaction volumes. Starnini et al. (2021) showed that velocity constraints allow these queries to bypass the full computational complexity of subgraph isomorphism.
The third is multi-signal sequence scoring. Once a candidate sequence is extracted, its suspiciousness cannot be assessed by any single feature. The convergence of several signals, velocity of the chain, homogeneity of amounts across hops, recurrence of intermediate accounts across multiple chains, and the modal direction of conversion, produces a composite score that is significantly more robust than any individual indicator.

Analyst reading guide:
The graph-based AML literature has converged on one consistent finding: suspicious financial behavior is structural and sequential, and detection systems that evaluate transactions in isolation systematically miss patterns that only become visible at the path level. Velocity, temporal order, and the directed flow of value between typed nodes are the signals that distinguish deliberate laundering sequences from ordinary transaction activity.
The transformation chain fits squarely within this research direction. What the existing literature has not yet addressed is the typed boundary constraint: the distinction between a generic relay chain and a sequence that begins with a typed injection event and terminates with a typed extraction event. That constraint is not a technical detail; it is what gives the pattern its criminal function in the MTO context, and it is what makes the modal direction of conversion analytically actionable.
The vulnerability of money transfer operators and mobile money platforms to layering abuse is well documented by international regulatory bodies, though the transformation chain as a named, formalized typology does not appear in any existing guidance.
FATF and MONEYVAL's joint report on money laundering through money remittance and currency exchange providers (2010) established the foundational typological framework for the sector, documenting that remittance businesses have been implicated in all three stages of the laundering cycle, placement, layering, and integration, and identifying rapid fund movement, minimal account dwell time, and sequential transfer patterns as primary red flags. The report predates the mobile money era but its structural observations remain directly applicable.
FATF's Risk-Based Approach Guidance for Money or Value Transfer Services (2016) places an explicit obligation on MVTS providers to implement transaction monitoring proportionate to their documented risk exposure, including the monitoring of P2P transfer activity as a high-risk channel due to the absence of underlying commercial purpose requirements.
FATF's Professional Money Laundering report (2018) documents the use of layered mule networks operating through MVTS infrastructure, describing sequential transfer chains used to distance criminal proceeds from their origin, a structural description that maps directly to the P2P relay layer of the transformation chain.
FinCEN's 2025 notice on financially motivated sextortion schemes provides an explicit operational description of fraud proceeds being layered through P2P platform mule accounts and subsequently withdrawn as cash, a direct parallel to the fraud variant of the transformation chain, described at the level of individual case typology without formal pattern naming.
TRACFIN's annual analysis (2024) identifies payment operators and mobile money platforms as high-risk channels for rapid sequential transactions with no declared economic purpose, noting the systematic use of cash-in followed by rapid peer transfers and cash-out as a recurring pattern in suspicious activity reports.
What is absent across all of these bodies of guidance is the formal recognition of the transformation chain as a pattern defined by its typed boundary events and the diagnostic significance of modal direction. No regulator currently identifies the CASHIN type and CASHOUT type combination as an autonomous risk indicator. No guidance specifies that the direction of conversion between injection and extraction events constitutes a signal for distinguishing money laundering from fraud-related activity. This gap has operational consequences: it means that the two criminal populations using the same structural pattern are likely to receive identical investigative treatment by compliance teams following existing guidance, resulting in suboptimal outcomes for both fraud recovery and money laundering prosecution.
The transformation chain presents a detection challenge that is architectural, not parametric. Raising thresholds, adding rules, or increasing manual review capacity does not address it. The pattern is designed to remain below every individual threshold. The only response that is structurally adequate is the capacity to execute typed path queries across a temporal transaction graph.
For a compliance or investigation team working within an MTO or mobile money operator, two questions determine whether the existing monitoring programme can surface this pattern.
The first: can the system reconstruct a directed path from a CASHIN event to a CASHOUT event through intermediate P2P transactions, bounded by a time window, and score the resulting sequence as a unit rather than as a set of individual events?
The second: when such a path is identified, does the system capture the modal direction of conversion, the event types at the injection and extraction endpoints, and use that information to differentiate between a potential AML case requiring upstream investigation and a potential fraud case requiring victim identification and downstream cash recovery?
If the answer to both is no, the two criminal populations using the transformation chain are passing undetected through the same infrastructure, at the same time, in opposite directions.
The pattern is not loud. It is not large. It is not unusual in any individual dimension. Its signal is structural, sequential, and directional. That is precisely what makes it durable.
© Thinsaction 2026 — No part of this article may be reproduced without attribution.