When Money Flows
in Circles


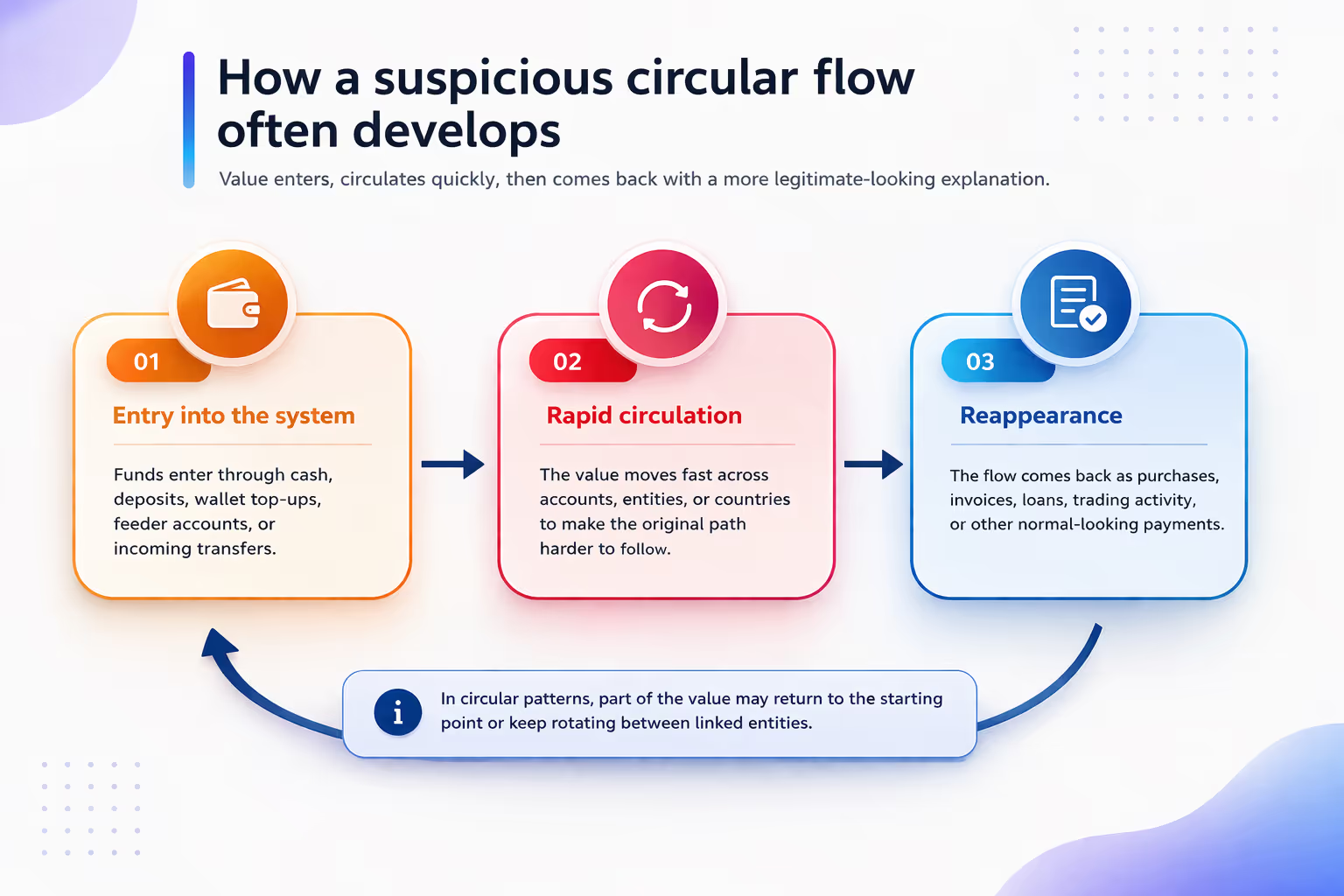
Circular flow means money or value moving through several accounts or entities and coming back to a related point, directly or indirectly. That does not automatically mean wrongdoing. Many normal business processes can look circular. But when the loop is too fast, too repetitive, too uniform, or too weakly justified, it becomes a strong signal of suspicious or anomalous activity.
Financial institutions care about these patterns because a circular path can break the intuitive story of a payment. Instead of value moving from a clear sender to a clear receiver for a clear reason, the flow starts to look like a loop, a relay race, or a boomerang. That is exactly why graph analytics and network-based monitoring have become so important in modern transaction monitoring programmes.
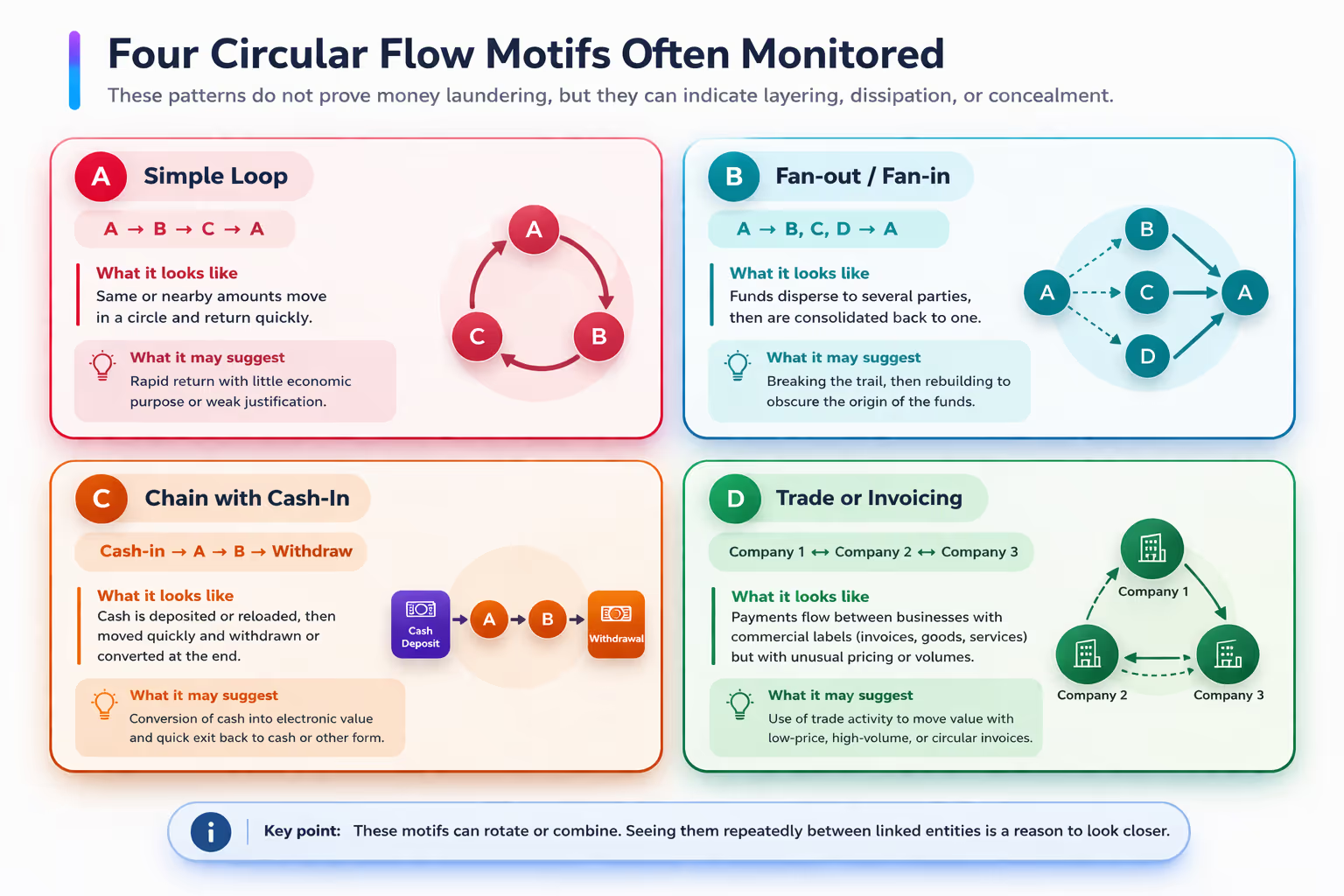
A circular flow is a movement of money that loops. The loop can be short, such as A -> B -> C -> A, or much larger, with many accounts, shell companies, payment channels, or countries in the middle. The money does not need to come back to the exact same account. It can return to the same beneficial owner, the same economic group, the same product chain, or the same control perimeter.
This matters because normal payments are usually easier to explain. Salary goes to an employee. A customer pays a merchant. A firm pays a supplier. In circular structures, the explanation often becomes thinner as the path gets more complex: many hops, very short delays, repeated round amounts, mirrored values, or business descriptions that sound acceptable but do not fully match the observed behavior.
From an operational point of view, loops are useful because they can blur the original source of value, spread it across entities, and then bring it back with a cleaner-looking narrative. A fast return after several hops can make one payment look like many unrelated payments. A fan-out followed by a fan-in can make one source look like a crowd. A commercial-looking payment can make a loop look like trade, treasury, or platform settlement.
Again, the point is not that every loop is improper. Large groups really do run internal transfers, treasury sweeps, cash concentration, and settlement chains. The challenge for a bank is to separate economically coherent loops from loops that have weak context, inconsistent counterparties, odd timing, or repeated structure across otherwise unrelated customers.
In real cases, circular structures are often not isolated. They are embedded inside a broader story: cash or top-up at the edge, rapid circulation through a small network, then conversion into a payment that looks more ordinary. The same pattern can also be combined with invoicing chains, correspondent transfers, nested relationships, wallet top-ups, marketplaces, or cross-border relays.
The red flags are usually behavioral rather than purely legal: speed without business reason, repeated reuse of the same path, very uniform amounts, bursts near reporting thresholds, multiple entities with little visible economic substance, and activity that only makes sense when seen as a network instead of one account at a time.
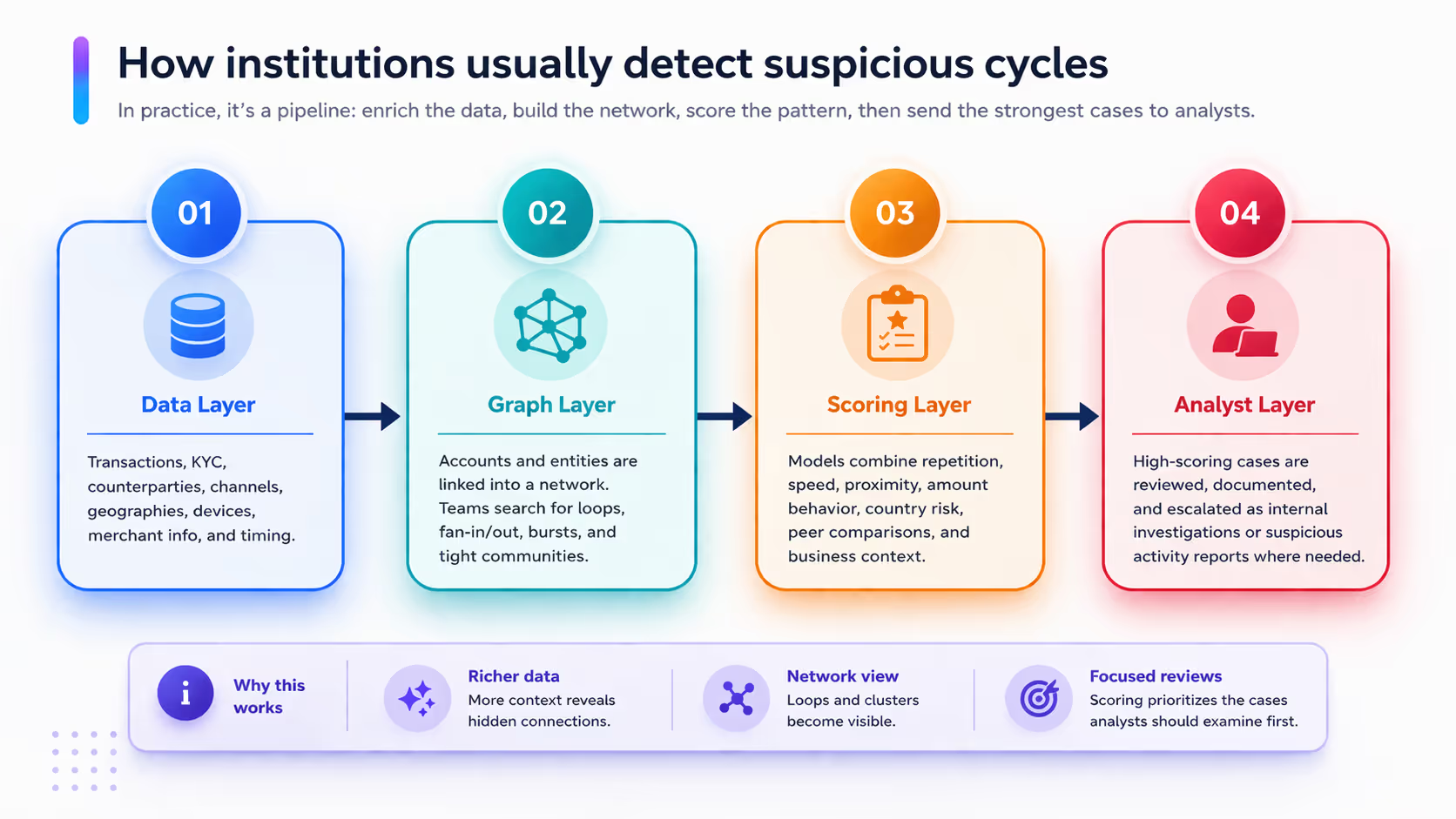
The state of the art has moved well beyond simple single-account rules. Most institutions still rely on rule scenarios, thresholds, and investigator review, but the strongest programmes now add graph features, peer comparisons, anomaly detection, entity resolution, and network scoring on top of the classical transaction monitoring stack.
In practical terms, detection usually starts by enriching payment data with KYC, ownership, geography, channels, device or merchant information, and timestamps. Then the institution builds a graph: nodes for customers, accounts, or companies; edges for payments, transfers, cash events, or business links. The system searches that graph for loops, near-loops, fan-out/fan-in structures, dense communities, and repeated motifs. Finally, the strongest cases are ranked and sent to analysts.
What features matter most?
Across the literature and industry guidance, the most informative features are surprisingly intuitive: loop length, return speed, amount similarity, repeated path reuse, degree of fan-out or fan-in, geographic spread, proximity to risky counterparties, mismatch with expected customer behavior, and the presence of weak or generic payment narratives. Many modern systems also use temporal features, graph embeddings, and community structure to spot patterns that are hard to encode as static rules.
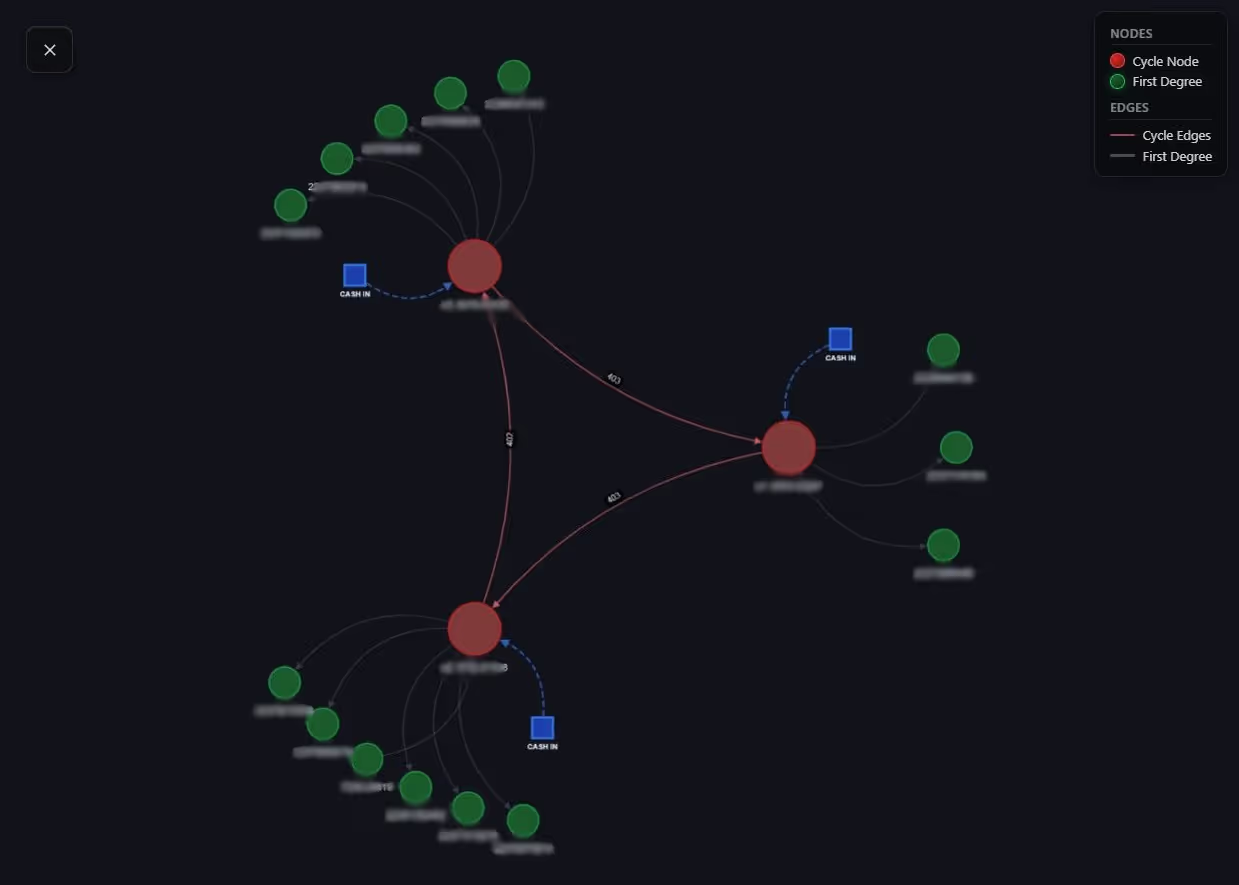
The detection result below illustrates what a cycle alert looks like in practice. The visual network highlights a closed loop across three key nodes, surrounded by first-degree connections. The panel on the right summarizes the signal: a critical risk label, 3 nodes, 3 transactions, a very short time span (0.02 days), and a final score of 0.91. In plain English, that means the system found a compact loop that moved quickly and matched several suspicious-cycle features at the same time.
How to read this result without over-interpreting it
Rule-based monitoring is still the backbone of many programmes because it is easy to audit and easy to operationalize. A bank can define scenarios such as short return cycles, repeated same-amount transfers, or rapid fan-out followed by fan-in. The downside is that fixed rules are brittle: they miss new patterns and generate many alerts on legitimate activity.
Graph analytics improves on this by looking at relationships instead of isolated transactions. It can detect subgraphs, loops, shared counterparties, central nodes, suspicious communities, and multi-hop paths that no single transaction would reveal on its own. This is especially useful when suspicious behavior is distributed across many small transfers.
Machine learning adds another layer. Supervised models learn from labeled cases, while unsupervised methods look for anomalies or unusual graph structures. More recent work uses graph neural networks, heterogeneous graphs, synthetic datasets, and temporal learning to model suspicious behavior more realistically. These approaches are promising, but they also raise familiar issues: poor labels, class imbalance, explainability, privacy constraints, and difficult model validation.
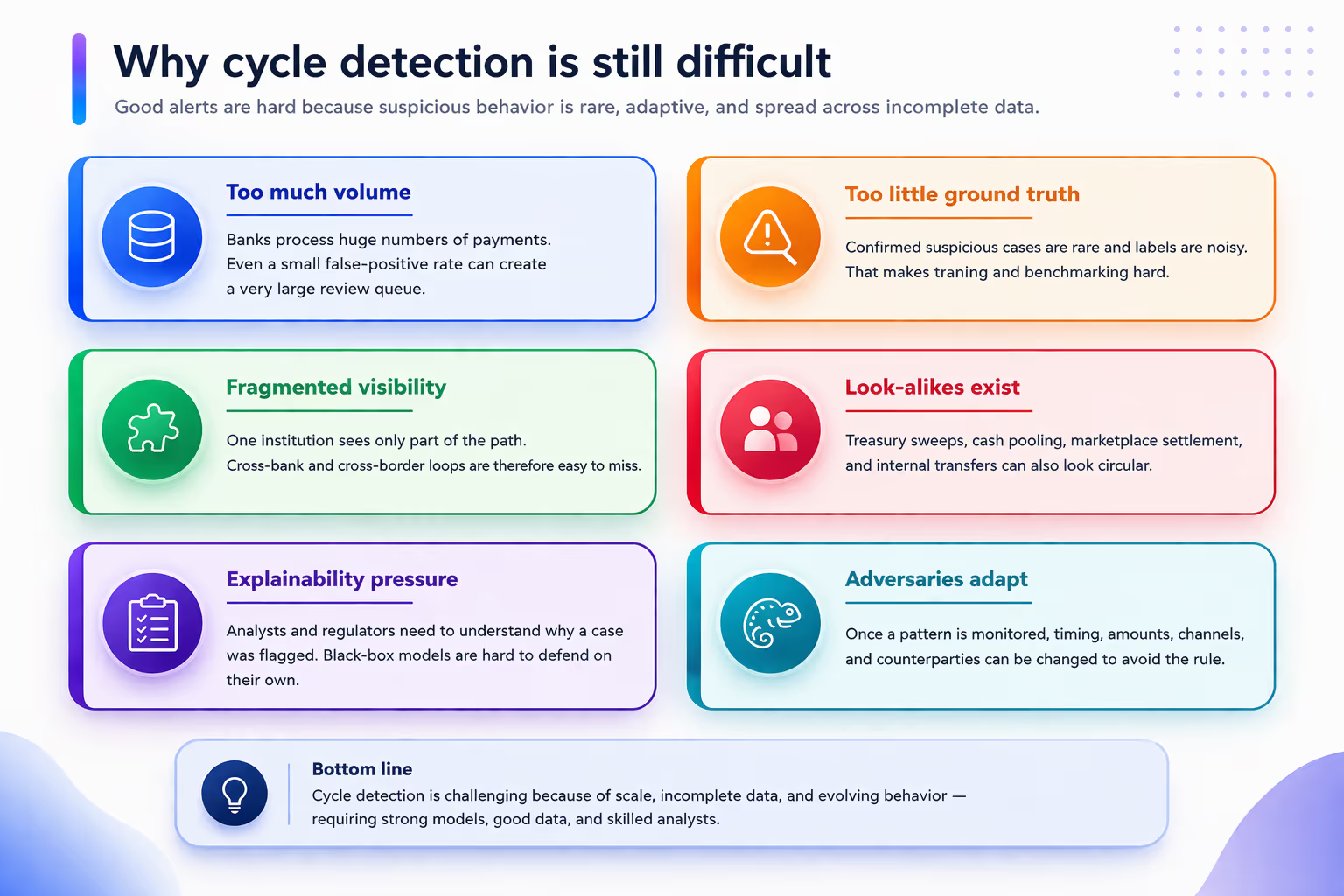
The first problem is scale. Real institutions process huge flows, while truly suspicious cases are rare. That creates an extreme imbalance problem: a model can be 'accurate' in a technical sense and still be operationally useless. This is why alert quality, review burden, and explainability matter as much as pure model performance.
The second problem is fragmented visibility. One institution may see only one leg of the path. The rest may sit in another bank, another payment service provider, another country, or another legal entity. That is one reason why collaborative analytics and data pooling are receiving so much attention in both policy work and innovation pilots.
The third problem is ambiguity. Many benign patterns look circular: internal treasury operations, cash concentration, platform settlement, and multi-entity group finance. A strong detection programme therefore needs network signals and business context at the same time. A loop without context is just geometry; a loop plus customer inconsistency is a much stronger case.
The fourth problem is adaptation. Once a pattern becomes known, it can be stretched, slowed down, split into smaller amounts, or mixed with normal flows. Detection is therefore a moving target. Good institutions constantly recalibrate scenarios, refresh graph features, and measure what investigators actually find useful.
The direction of travel is clear. The industry is moving from isolated alerts to network-aware monitoring, from static thresholds to dynamic scoring, and from single-institution visibility to more privacy-aware forms of collaboration. Projects such as Aurora and Hertha show the value of combining payment analytics, data minimization, and cross-entity pattern detection. At the research level, graph learning, temporal models, and synthetic benchmark data are helping teams test methods that were previously hard to compare fairly.
For a blog reader, the key takeaway is simple: suspicious circular flow is not just 'money going around'. It is a pattern where the path itself becomes meaningful. When value moves in circles too quickly, too neatly, or without a credible business story, the circle becomes a signal. Modern detection systems try to turn that signal into a prioritized investigation, while avoiding the trap of flagging every loop that happens to be legitimate.
[1] FATF. International Standards on Combating Money Laundering and the Financing of Terrorism & Proliferation (FATF Recommendations). Updated 2025.
[2] FATF. Stocktake on Data Pooling, Collaborative Analytics and Data Protection. 2021.
[3] FATF. Money Laundering and Terrorist Financing in the Securities Sector. 2009.
[4] European Banking Authority. Final Amending Guidelines on ML/TF Risk Factors. 2024.
[5] European Banking Authority. Joint Guidelines to Prevent Terrorist Financing and Money Laundering in Electronic Fund Transfers. 2017.
[6] Wolfsberg Group. Payment Transparency Standards. 2023.
[7] Wolfsberg Group. Transaction Monitoring Request for Information Best Practice Guidance. 2022.
[8] Wolfsberg Group. Statement on Developing an Effective AML/CTF Programme. 2020.
[9] SWIFT Institute. Better Ways to Detect and Disrupt Financial Crime. 2020.
[10] BIS Innovation Hub. Project Aurora. 2023.
[11] BIS Innovation Hub. Project Hertha. 2025.
[12] Desai, A., Kosse, A., and Sharples, J. Finding a Needle in a Haystack: A Machine Learning Framework for Anomaly Detection in Payment Systems. BIS Working Papers No. 1188, 2024.
[13] Broeders, D., and Prenio, J. Suptech Applications for Anti-Money Laundering. BIS FSI Insights, No. 18, 2018.
[14] Oztas, B. Transaction Monitoring in Anti-Money Laundering: A Qualitative Analysis and Points of View from Industry. Future Generation Computer Systems, 2024.
[15] Silva, I. D. G., Correia, L. H. A., and Maziero, E. G. Graph Neural Networks Applied to Money Laundering Detection in Intelligent Information Systems. Proceedings of the XIX Brazilian Symposium on Information Systems, 2023.
[16] Schmidt, J., Pasadakis, D., Sathe, M., and Schenk, O. GAMLNet: A Graph-Based Framework for the Detection of Money Laundering. 2024 IEEE Swiss Conference on Data Science, 2024.
[17] Johannessen, F., and Jullum, M. Finding Money Launderers Using Heterogeneous Graph Neural Networks. Journal of Finance and Data Science, 2025.
[18] Bakhshinejad, N., Nguyen, U. T., Ghahremani, S., and Soltani, R. A Graph-Based Deep Learning Model for the Anti-Money Laundering Task of Transaction Monitoring. 2024.
[19] Altman, E., et al. Realistic Synthetic Financial Transactions for Anti-Money Laundering Models. NeurIPS Datasets and Benchmarks, 2023.
[20] Deep Learning Approaches for Anti-Money Laundering on Mobile Transactions: Review, Framework, and Directions. arXiv, 2025.
© Thinsaction 2026 — No part of this article may be reproduced without attribution.